Submitted:
05 September 2024
Posted:
05 September 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
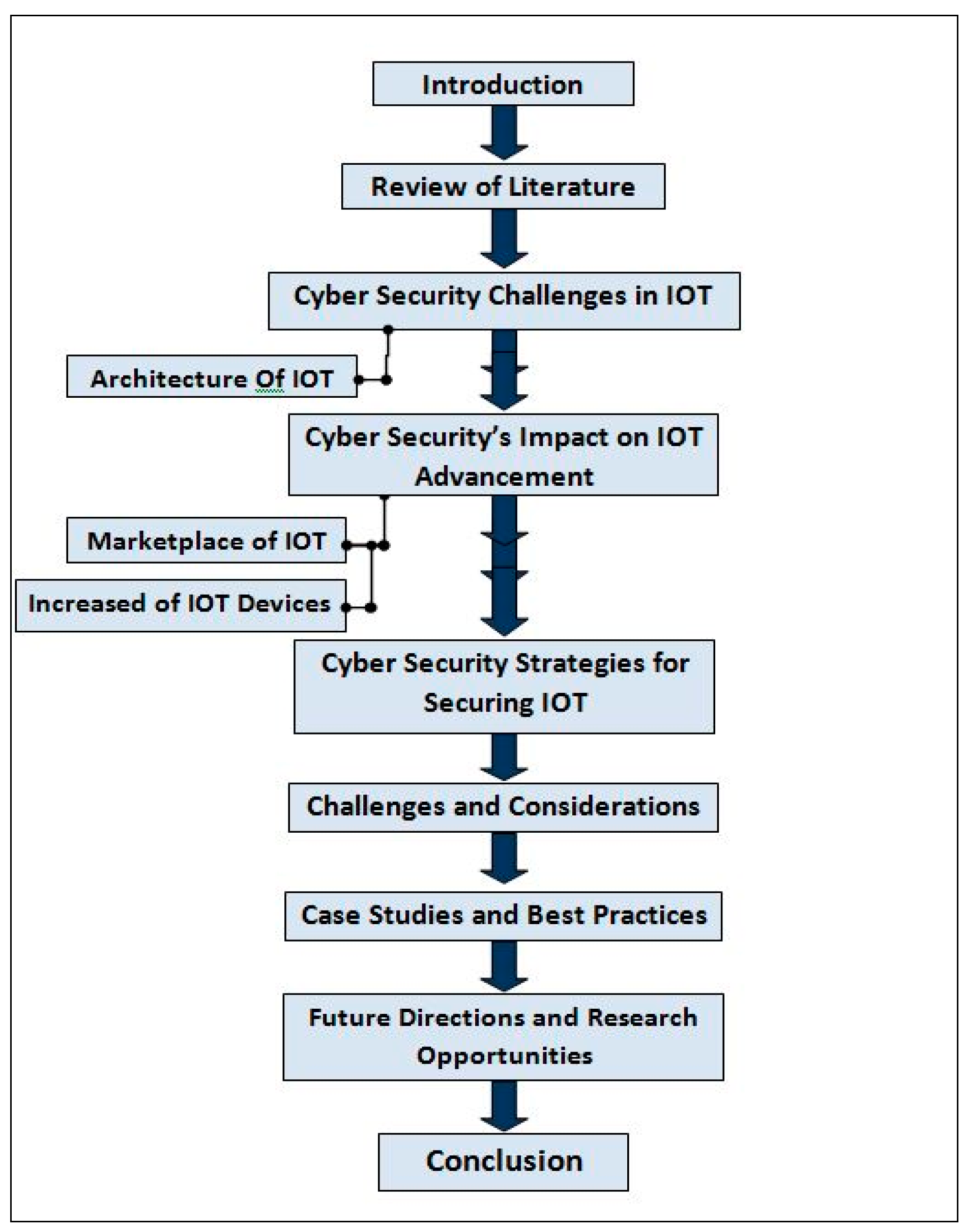
2. Review of Literature
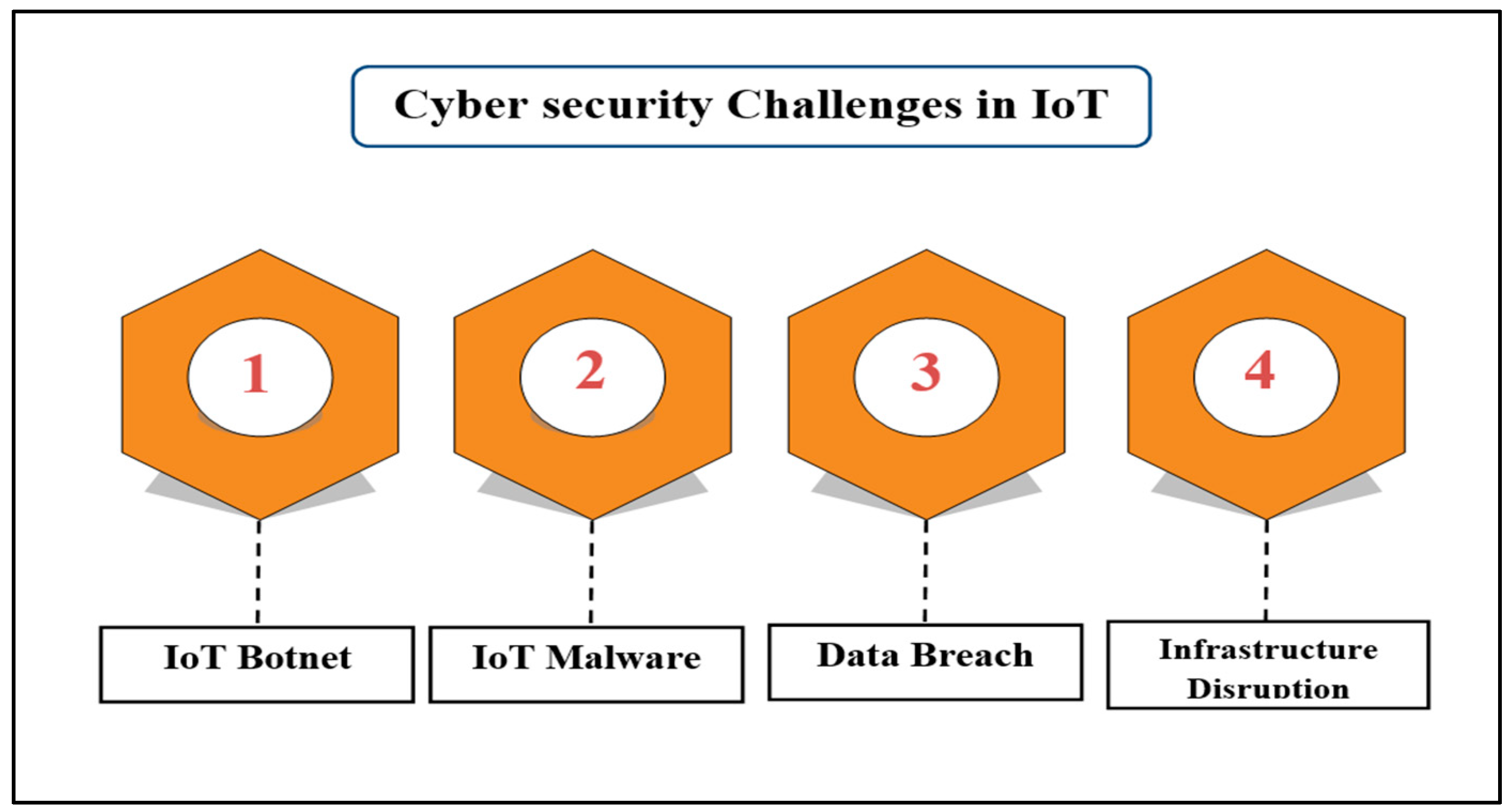
3. IoT Cybersecurity Challenges
- Botnet for the Internet of Things: A network of compromised devices under centralized command is called a botnet. Cybercriminals utilize botnets to automate massive assaults including distributed denial-of-service (DDoS) attacks, crypto mining, virus dissemination, and data theft.
- Internet of Things Malware: Through attacks on IoT devices, a range of malicious software aims to compromise the security and integrity of the Internet of Things ecosystem. It is designed to exploit flaws in Internet of Things devices, such as firmware instability, default settings, and unpatched software.
- Data Breach: Wide-ranging effects could result from a breach in the Internet of Things (IoT) ecosystem, affecting vital industries including infrastructure, finance, and healthcare. Secure data or operational systems could pose a serious threat to national security, public safety, and economic stability.
- Infrastructure Disruption: Cyberattacks aimed at the Internet of Things (IoT) ecosystem have the potential to compromise vital services and vital infrastructure, such as energy grids, transportation networks, and medical institutions. Furthermore, ransomware attacks and DDoS attacks that target network infrastructure and operational systems, respectively, can happen.
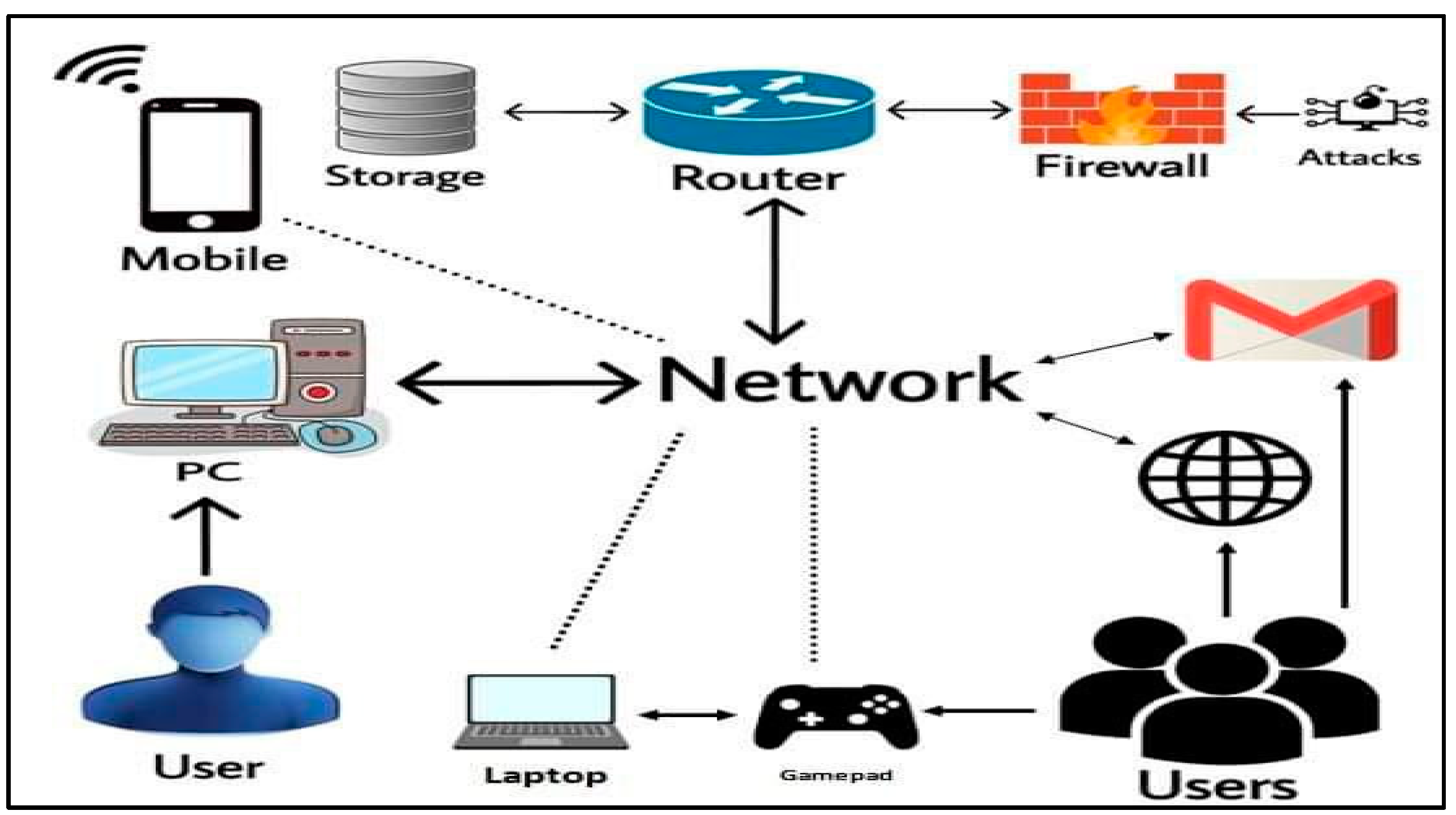
Architecture of IoT
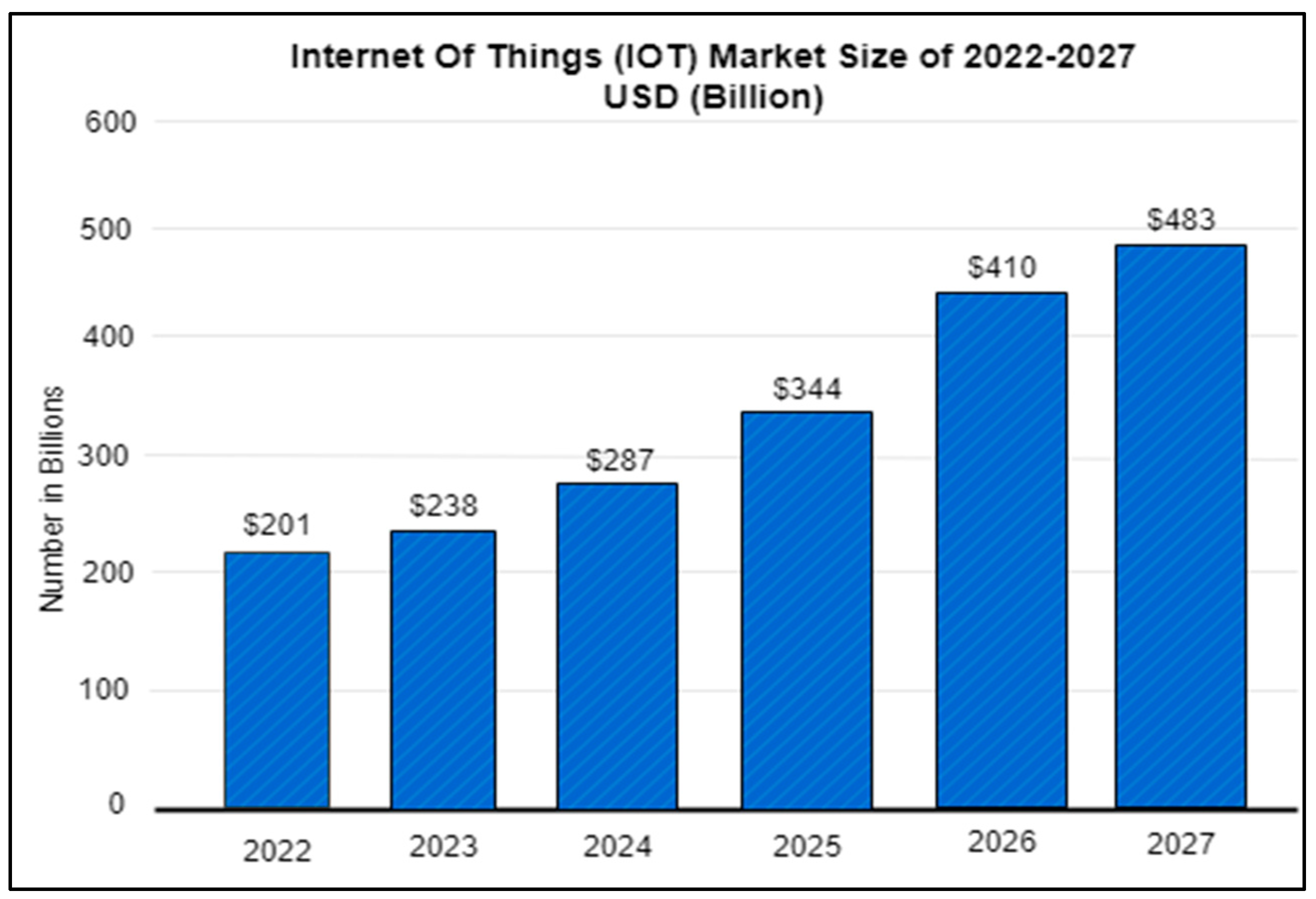
4. Cyber Security's Impact on IoT Advancement
- Faith and Self-Belief: Stakeholders in IoT technology, organizations and consumers all gain confidence and trust from effective cyber security safeguards.
- Risk Mitigation: Cyber security plays a key role in reducing the risks that come with Internet of Things deployments, such as infrastructure failures, privacy violations, and data breaches. Through vulnerability identification and remediation, preventive measures implementation, and adherence to best practices, companies can reduce the probability and effect of cyber threats directed toward IoT ecosystems.
- Investment and Innovation: By fostering a climate that is favorable for research, development, and commercialization, cyber security encourages innovation and investment in IoT technology. Businesses that put cyber securityfirst stand out from the competition, draw capital, and spur innovation in fields like threat intelligence, secure hardware, and encryption technologies.
- Regulatory Compliance: The development of IoT depends on adherence to industry standards and cyber security laws. Regulations and rules for safeguarding IoT devices, controlling cyber security risks, and preserving data privacy are established by regulatory frameworks including the General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), and cyber security standards like ISO/IEC 27001.
- Security of the Supply Chain: Cyber security now covers every link in the supply chain, from manufacturers to suppliers to service providers, and goes beyond individual IoT devices. The implementation of secure supply chain procedures, such as vendor vetting, software integrity assurance, and supply chain resilience measures, can improve the credibility and dependability of Internet of Things products and services.
5. Cyber Security Strategies for Securing IoT
6. Challenges and Considerations
- Scalability Issues: Managing an increasing number of IoT devices is becoming more challenging. This entails maintaining data privacy, secure communication, and reliable performance on all devices.
- Security Frameworks: For real-time threat detection and mitigation in Internet of Things networks, a thorough security framework is necessary. Hardware-based security modules, zero trust architecture, and real-time response based on Node MCU ESP8266 are a few examples of such a framework.
- Proactive Measures: Resolving security issues calls for a multifaceted, proactive strategy that includes ongoing monitoring, risk analysis, and modification of security measures in response to ecosystem changes.
7. Case Studies and Best Practices
8. Future Directions and Research Opportunities
9. Conclusion
References
- Lee, I. Internet of Things (IoT) cybersecurity: Literature review and IoT cyber risk management. Future Internet 2020, 12, 157. [Google Scholar] [CrossRef]
- Strecker, S.; Van Haaften, W.; Dave, R. An analysis of IoT cyber security driven by machine learning. In Proceedings of International Conference on Communication and Computational Technologies: ICCCT 2021; Springer: Singapore, 2021; pp. 725–753. [Google Scholar]
- Kotenko, I.; Izrailov, K.; Buinevich, M. Static analysis of information systems for IoT cyber security: A survey of machine learning approaches. Sensors 2022, 22, 1335. [Google Scholar] [CrossRef] [PubMed]
- Nock, O.; Starkey, J.; Angelopoulos, C.M. Addressing the security gap in IoT: towards an IoT cyber range. Sensors 2020, 20, 5439. [Google Scholar] [CrossRef] [PubMed]
- Sivanathan, A.; Gharakheili, H.H.; Sivaraman, V. Managing IoT cyber-security using programmable telemetry and machine learning. IEEE Transactions on Network and Service Management 2020, 17, 60–74. [Google Scholar] [CrossRef]
- Djenna, A.; Harous, S.; Saidouni, D.E. Internet of ThingsmeetsInternet of Threats: New concern Cyber security issues of critical cyber infrastructure. Applied Sciences 2021, 11, 4580. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Friha, O.; Maglaras, L.; Janicke, H.; Shu, L. Federated deep learning for cyber security in the internet of things: Concepts, applications, and experimental analysis. IEEE Access 2021, 9, 138509–138542. [Google Scholar] [CrossRef]
- Ashraf, I.; Park, Y.; Hur, S.; Kim, S.W.; Alroobaea, R.; Zikria, Y.B.; Nosheen, S. A survey on cyber security threats in IoT-enabled maritime industry. IEEE Transactions on Intelligent Transportation Systems 2022, 24, 2677–2690. [Google Scholar] [CrossRef]
- Kotenko, I.; Izrailov, K.; Buinevich, M. Static analysis of information systems for IoT cyber security: A survey of machine learning approaches. Sensors 2022, 22, 1335. [Google Scholar] [CrossRef]
- Alterazi, H.A.; Kshirsagar, P.R.; Manoharan, H.; Selvarajan, S.; Alhebaishi, N.; Srivastava, G.; Lin, J.C.W. Prevention of cyber security with the Internet of Things using particle swarm optimization. Sensors 2022, 22, 6117. [Google Scholar] [CrossRef]
- Ganai, P.T.; Bag, A.; Sable, A.; Abdullah, K.H.; Bhatia, S.; Pant, B. A Detailed Investigation of Implementation of Internet of Things (IoT) in Cyber Security in the Healthcare Sector. In 2022 2nd International Conference on Advance Computing and Innovative Technologies in Engineering (ICACITE); IEEE, April 2022; pp. 1571–1575. [Google Scholar]
- Ferrag, M.A.; Friha, O.; Hamouda, D.; Maglaras, L.; Janicke, H. Edge-IIoTset: A new comprehensive realistic cyber security dataset of IoT and IoT applications for centralized and federated learning. IEEE Access 2022, 10, 40281–40306. [Google Scholar] [CrossRef]
- Lone, A.N.; Mustajab, S.; Alam, M. A comprehensive study on cybersecurity challenges and opportunities in the IoT world. Security and Privacy 2023, 6, e318. [Google Scholar] [CrossRef]
- Raimundo, R.J.; Rosário, A.T. Cybersecurity in the Internet of Things in industrial management. Applied Sciences 2022, 12, 1598. [Google Scholar] [CrossRef]
- Tyagi, A.K. Blockchain and Artificial Intelligence for Cyber Security in the Era of Internet of Things and Industrial Internet of Things Applications. In AI and Blockchain Applications in Industrial Robotics; IGI Global, 2024; pp. 171–199. [Google Scholar]
- Rekeraho, A.; Cotfas, D.T.; Cotfas, P.A.; Bălan, T.C.; Tuyishime, E.; Acheampong, R. Cybersecurity challenges in IoT-based smart renewable energy. International Journal of Information Security 2024, 23, 101–117. [Google Scholar] [CrossRef]
- Kumari, S.; Tulshyan, V.; Tewari, H. Cyber Security on the Edge: Efficient Enabling of Machine Learning on IoT Devices. Information 2024, 15, 126. [Google Scholar] [CrossRef]
- Qamar, R.; Zardari, B.A.; Khang, A. Cyber Security for Internet of Things (IoT) Devices and Sensors. In Agriculture and Aquaculture Applications of Biosensors and Bioelectronics; IGI Global, 2024; pp. 441–457. [Google Scholar]
- Dhabliya, D.; Pandey, P.; Agarwal, V.; Gobi, N.; Dhablia, A.; Kumar, J.R.R.; Gupta, A.; Pramanik, S. Suggested Cyber-Security Strategy That Maximizes Automated Detection of Internet of Things Attacks Using Machine Learning. In Methodologies, Frameworks, and Applications of Machine Learning; IGI Global, 2024; pp. 187–200. [Google Scholar]
- Inuwa, M.M.; Das, R. A comparative analysis of various machine learning methods for anomaly detection in cyberattacks on IoT networks. Internet of Things 2024, 26, 101162. [Google Scholar] [CrossRef]
- Khan, M.A. Challenges facing the application of IoT in medicine and healthcare. International Journal of Computations, Information and Manufacturing (IJCIM) 2021, 1. [Google Scholar] [CrossRef]
- Farooq, M.S.; Abdullah, M.; Riaz, S.; Alvi, A.; Rustam, F.; Flores, M.A.L.; Galán, J.C.; Samad, M.A.; Ashraf, I. A survey on the role of industrial IoT in manufacturing for implementation of smart industry. Sensors 2023, 23, 8958. [Google Scholar] [CrossRef]
- Taj, S.; Imran, A.S.; Kastrati, Z.; Daudpota, S.M.; Memon, R.A.; Ahmed, J. IoT-based supply chain management: A systematic literature review. Internet of Things 2023, 24, 100982. [Google Scholar] [CrossRef]
- Nguyen, H.; Nawara, D.; Kashef, R. Connecting the Indispensable Roles of IoT and Artificial Intelligence in Smart Cities: A Survey. Journal of Information and Intelligence 2024. [Google Scholar] [CrossRef]
- Jami Pour, M.; Hosseinzadeh, M.; Moradi, M. IoT-based entrepreneurial opportunities in smart transportation: a multidimensional framework. International Journal of Entrepreneurial Behavior & Research 2024, 30, 450–481. [Google Scholar]
- Deshmukh, A.; Patil, D.S.; Pawar, P.D.; Kumari, S.; Muthulakshmi, P. Recent Trends for Smart Environments With AI and IoT-Based Technologies: A Comprehensive Review. In Handbook of Research on Quantum Computing for Smart Environments; 2023; pp. 435–452. [Google Scholar]
- Uddin, M.A.; Stranieri, A.; Gondal, I.; Balasubramanian, V. A survey on the adoption of blockchain in IoT: Challenges and solutions. Blockchain: Research and Applications 2021, 2, 100006. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



