Submitted:
13 October 2024
Posted:
14 October 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Related Works
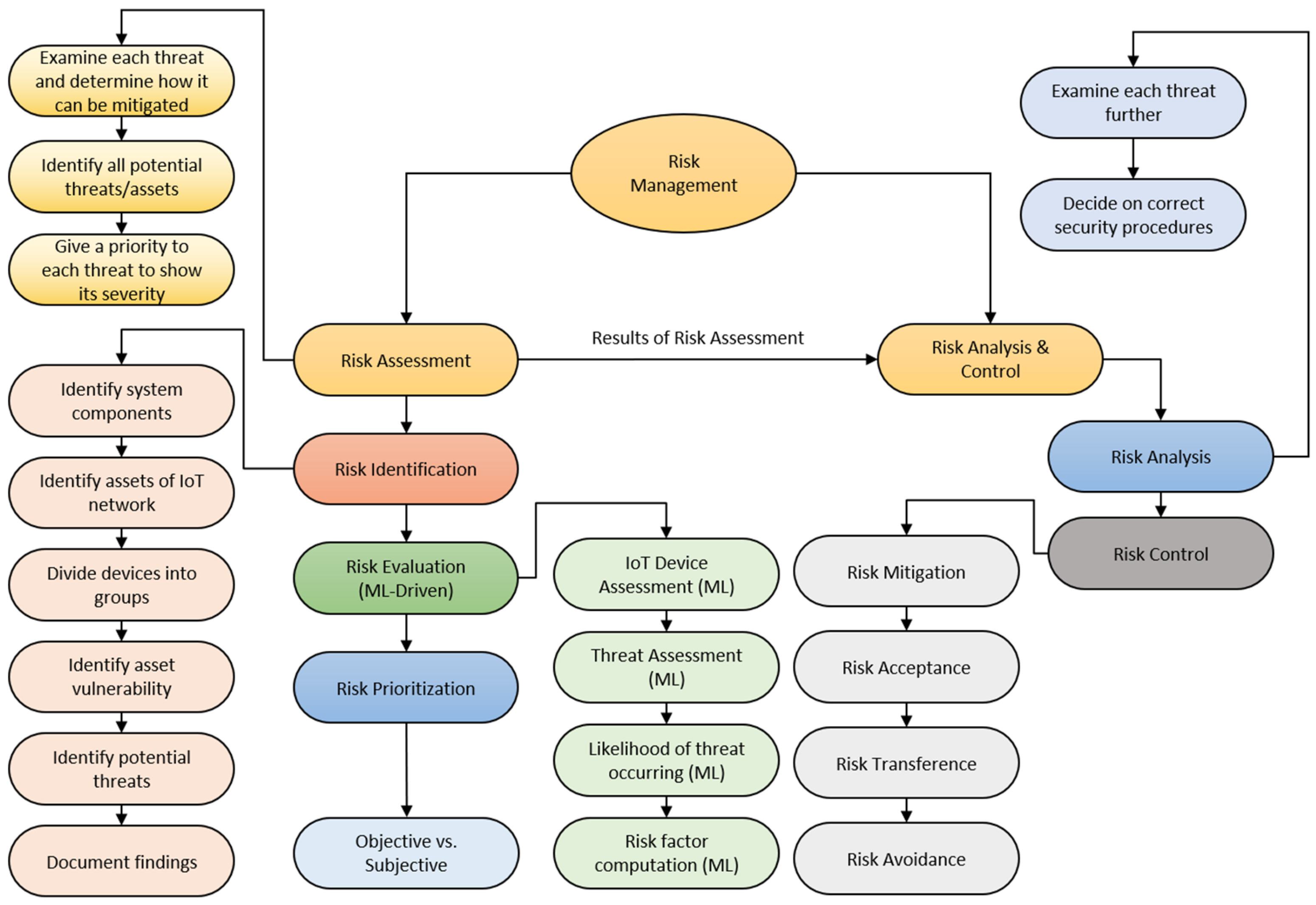
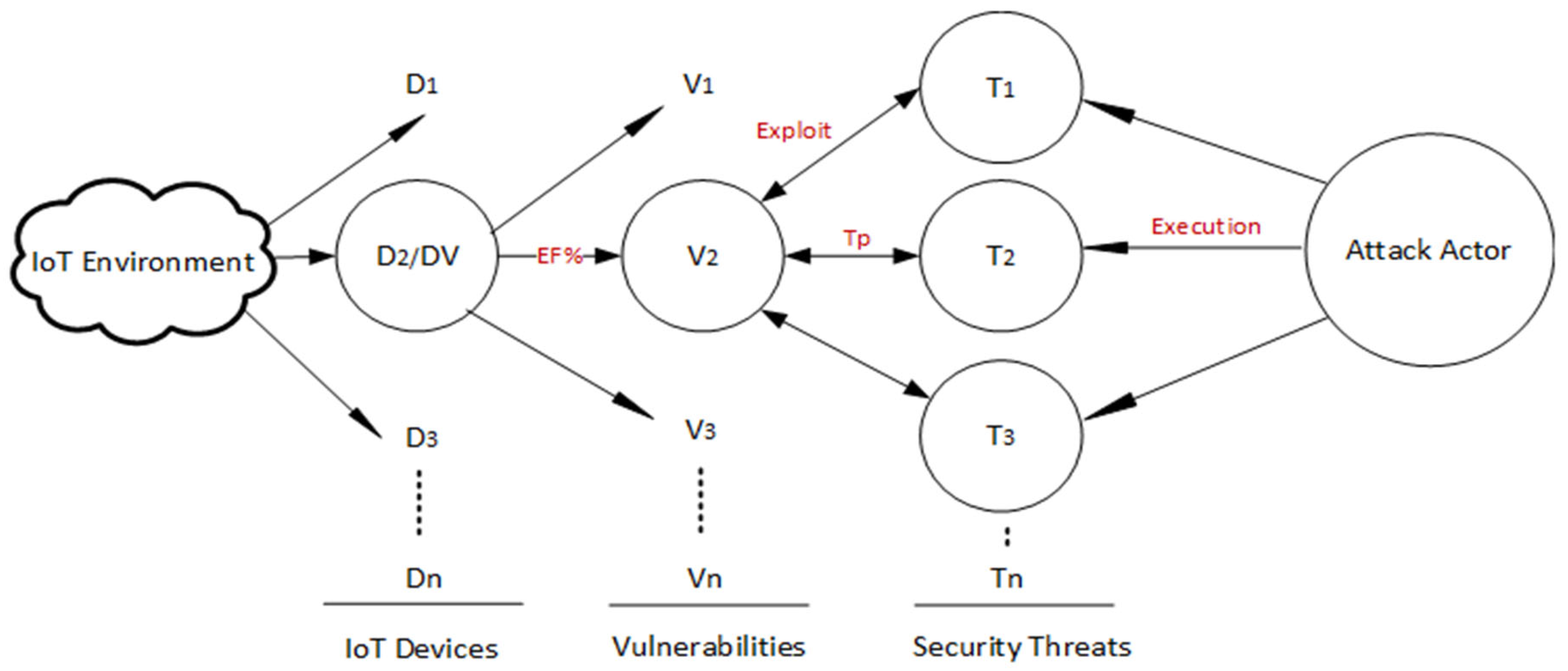
3. Proposed Risk Management (RM) Framework for IoT Devices and Networks
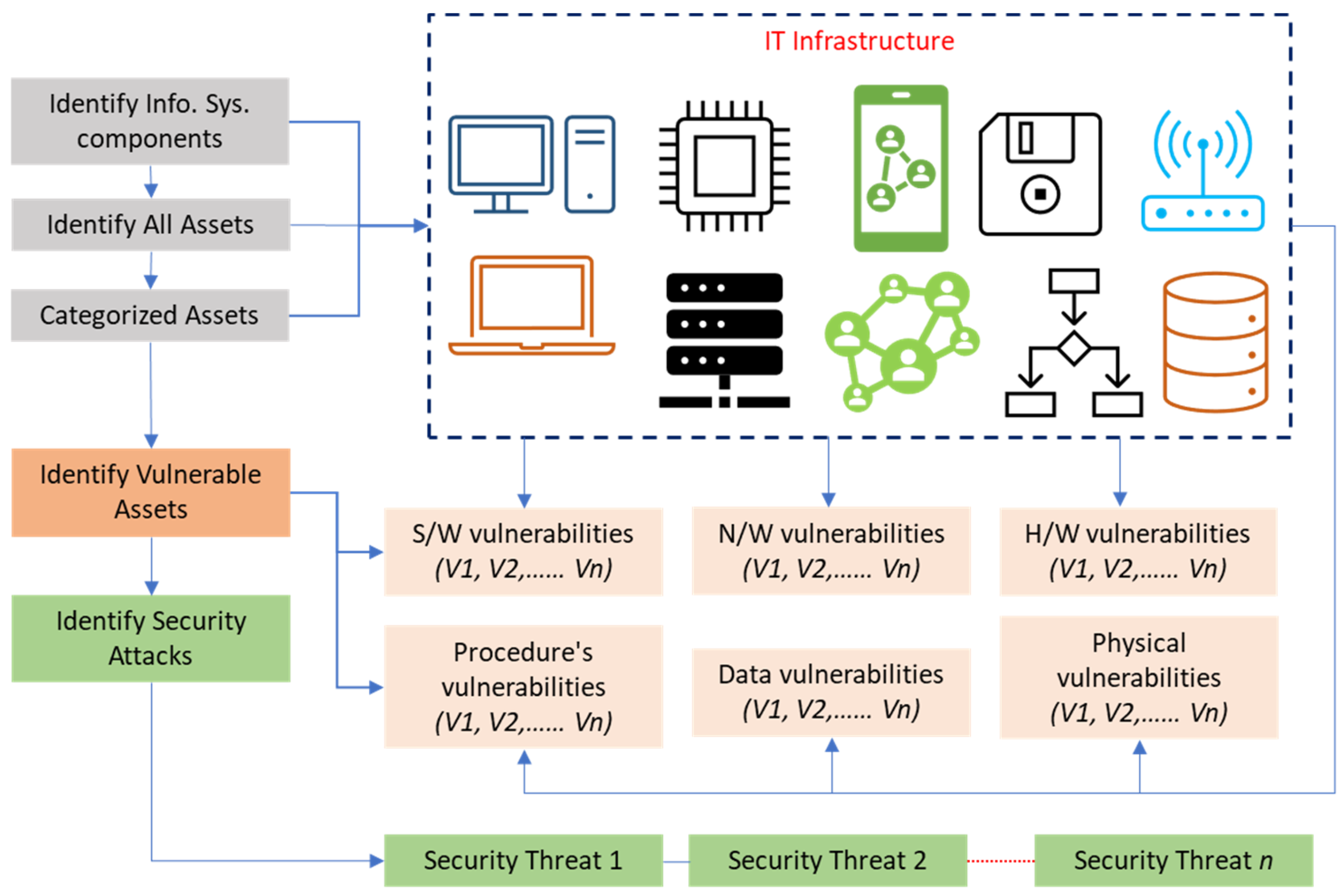
3.1. Risk Identification
3.1.1. Identify IoT Network Components and Assets
3.1.2. Divide IoT Devices into Groups
3.1.3. Identification of Vulnerable Assets and Potential Security Threats
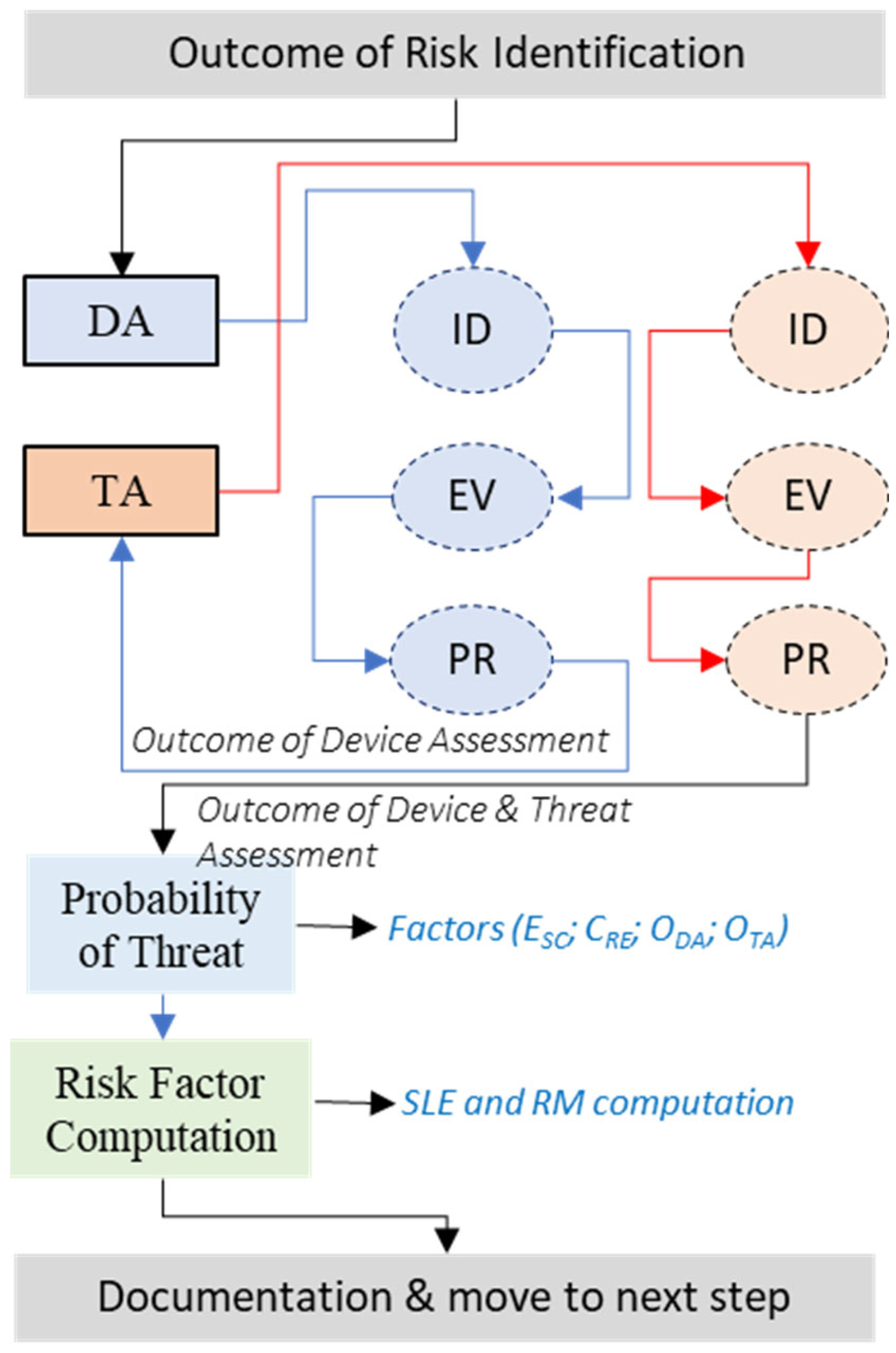
3.2. Risk Evaluation
3.2.1. IoT Device Assessment (DA)
- A.
- Template Questions for DA
- B.
- Explanation of DA Template Questions
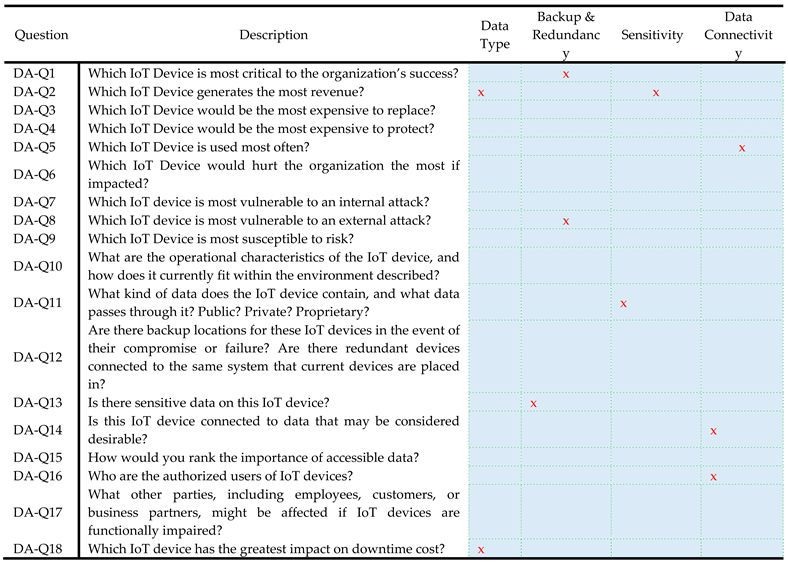
- C.
- Device Score Computation
3.2.2. IoT Threat Assessment (TA)
- A.
- Template Questions for TA
- B.
- Explanation of TA Template Questions
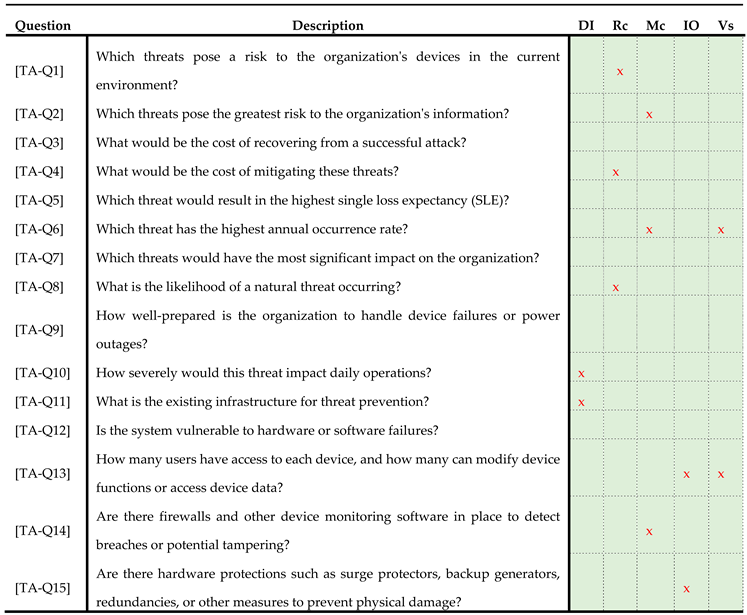
- C.
- Threat Score Computation
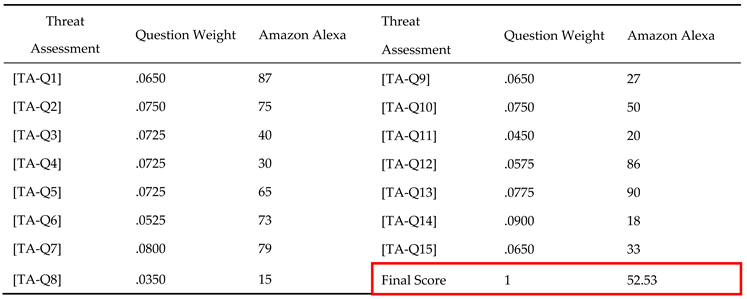
- Ts: Threat Score, which is the final score assigned to the identified threat.
- TAQi: Threat Assessment Question (TAQ) score for each criterion. This score represents the evaluation of the threat based on a specific criterion.
- Wi: Weight assigned by the SMG to each criterion i. This weight reflects the relative importance or preference given to the criterion during the threat assessment process.
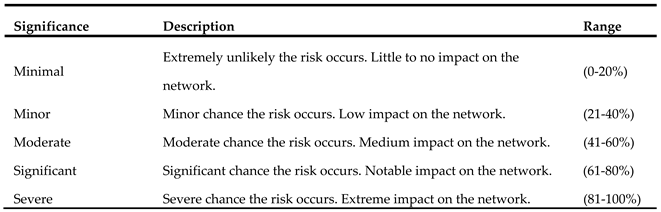
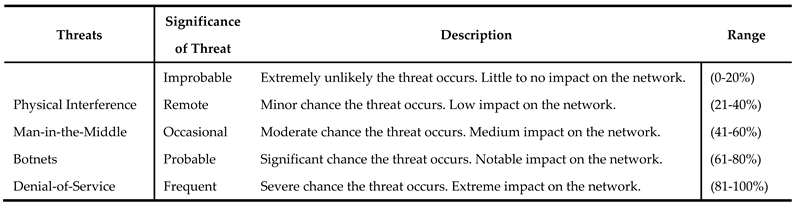
3.2.3. Likelihood of Threat Occurring
3.2.4. Risk Factor Computations
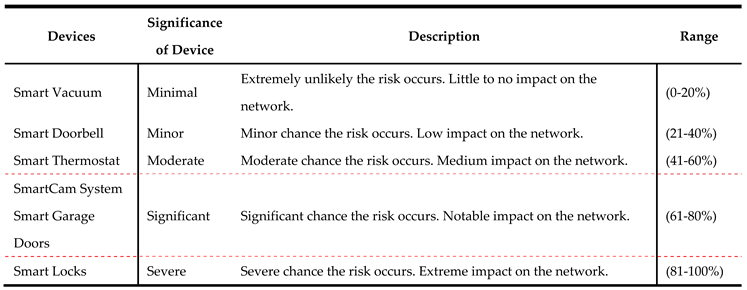
3.3. Risk Prioritization
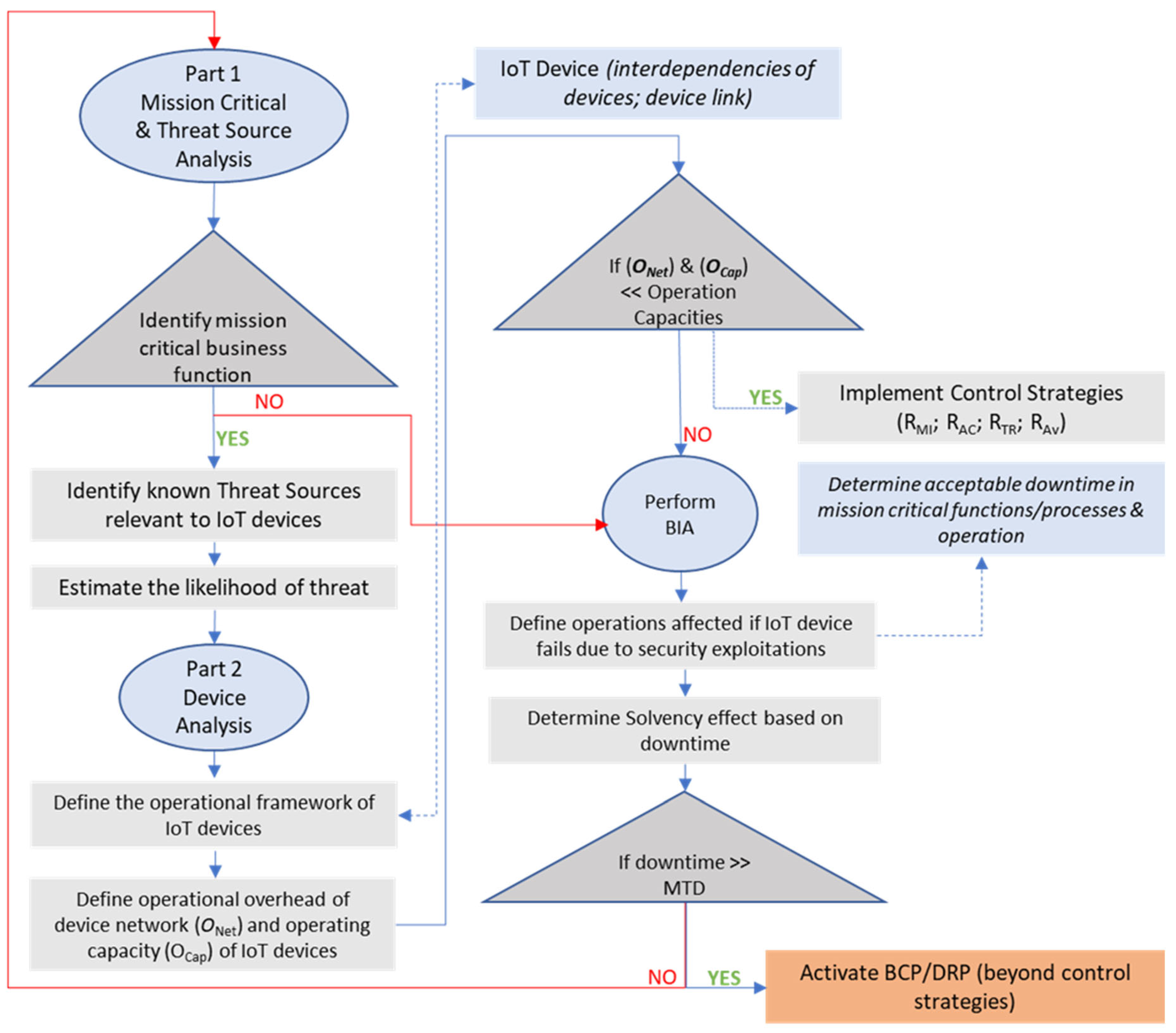
3.4. Risk Analysis
3.4.1. Part 1: Mission-Critical and Threat Source Analysis
3.4.2. Part 2: Device Analysis
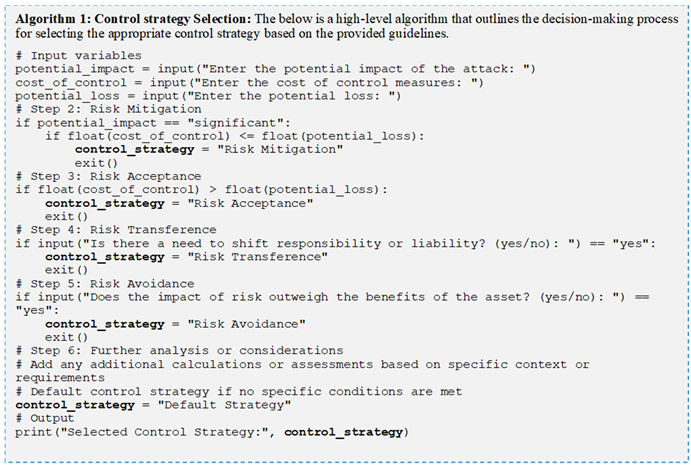
3.5. Risk Control
3.5.1. Control Strategies
4. Implementation of the Proposed RM Framework Using Case Studies
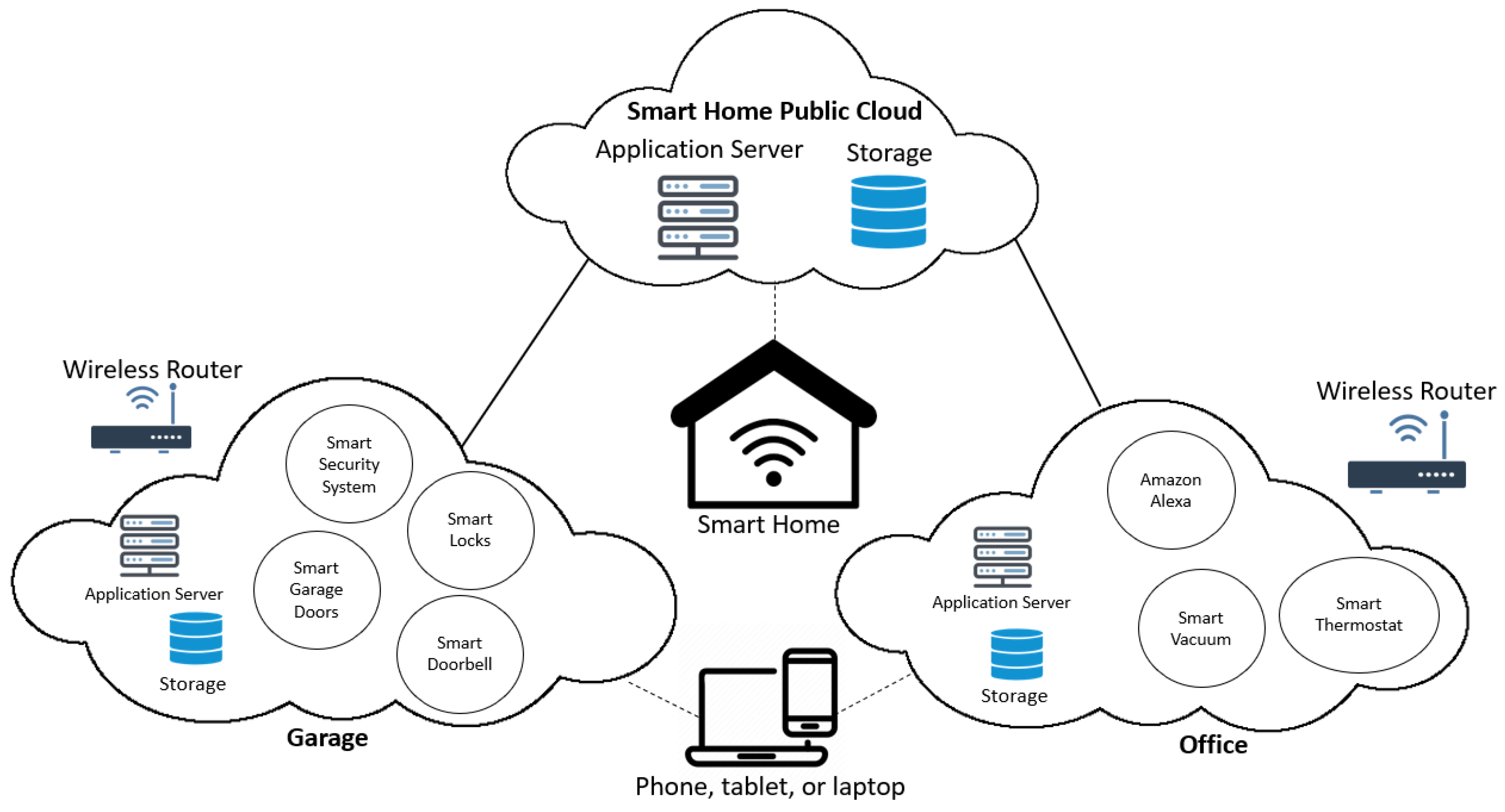
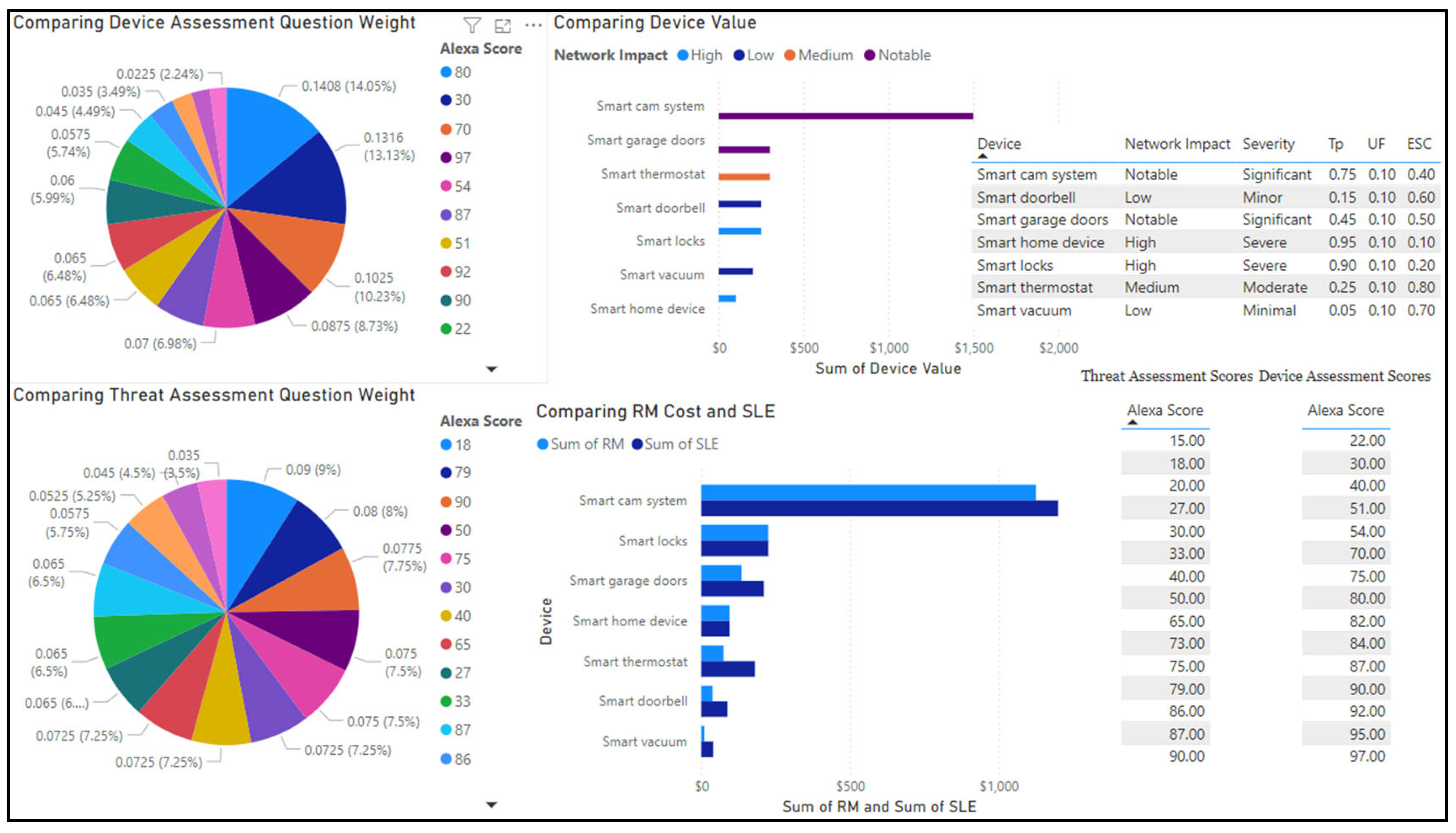
4.1. Smart Home Scenario
4.1.1. Risk Identification of the Smart Home Network
4.1.2. Risk Evaluation of the Smart Home Network
- A.
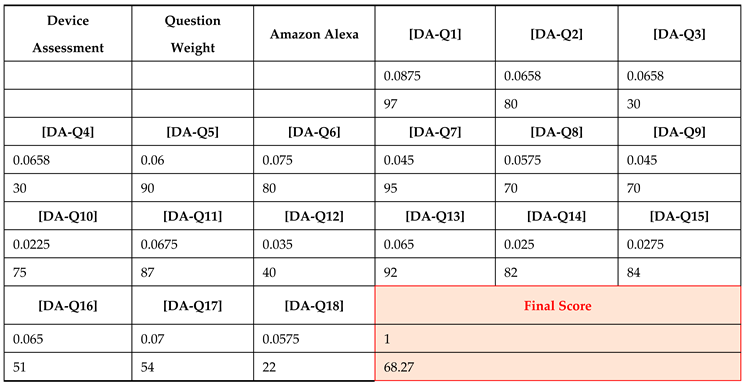
- Device Assessment (DA)
- Smart home device (Amazon Alexa) [DA-Q1],[DA-Q5],[DA-Q6],[DA-Q12],[DA-Q13]
- Smart locks [DA-Q16] [DA-Q17]
- Smart cam system (security system) [DA-Q14], [DA-Q15]
- Smart garage doors [DA-Q3]
- Smart thermostat [DA-Q17]
- Smart doorbell [DA-Q14]
- B.
- Threat Assessment (TA)
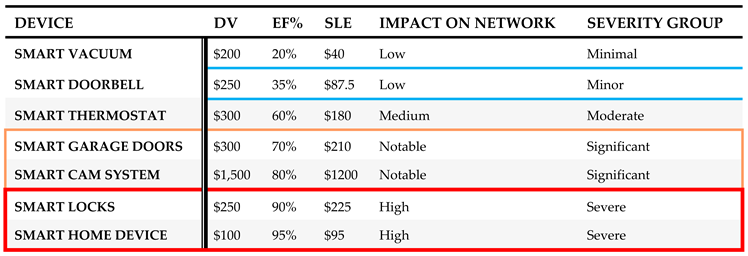
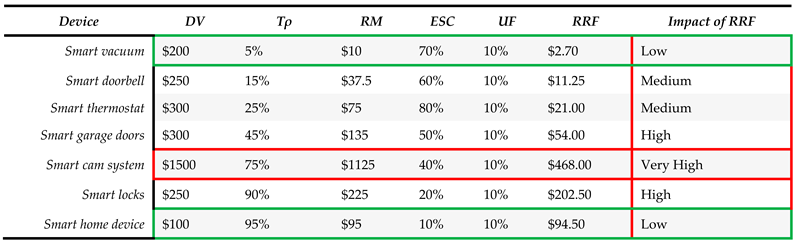
4.1.3. Risk Factor Computations and Prioritization
4.1.4. Risk Analysis of Smart Home IoT Devices
4.1.5. Risk Control of Smart Home IoT Devices
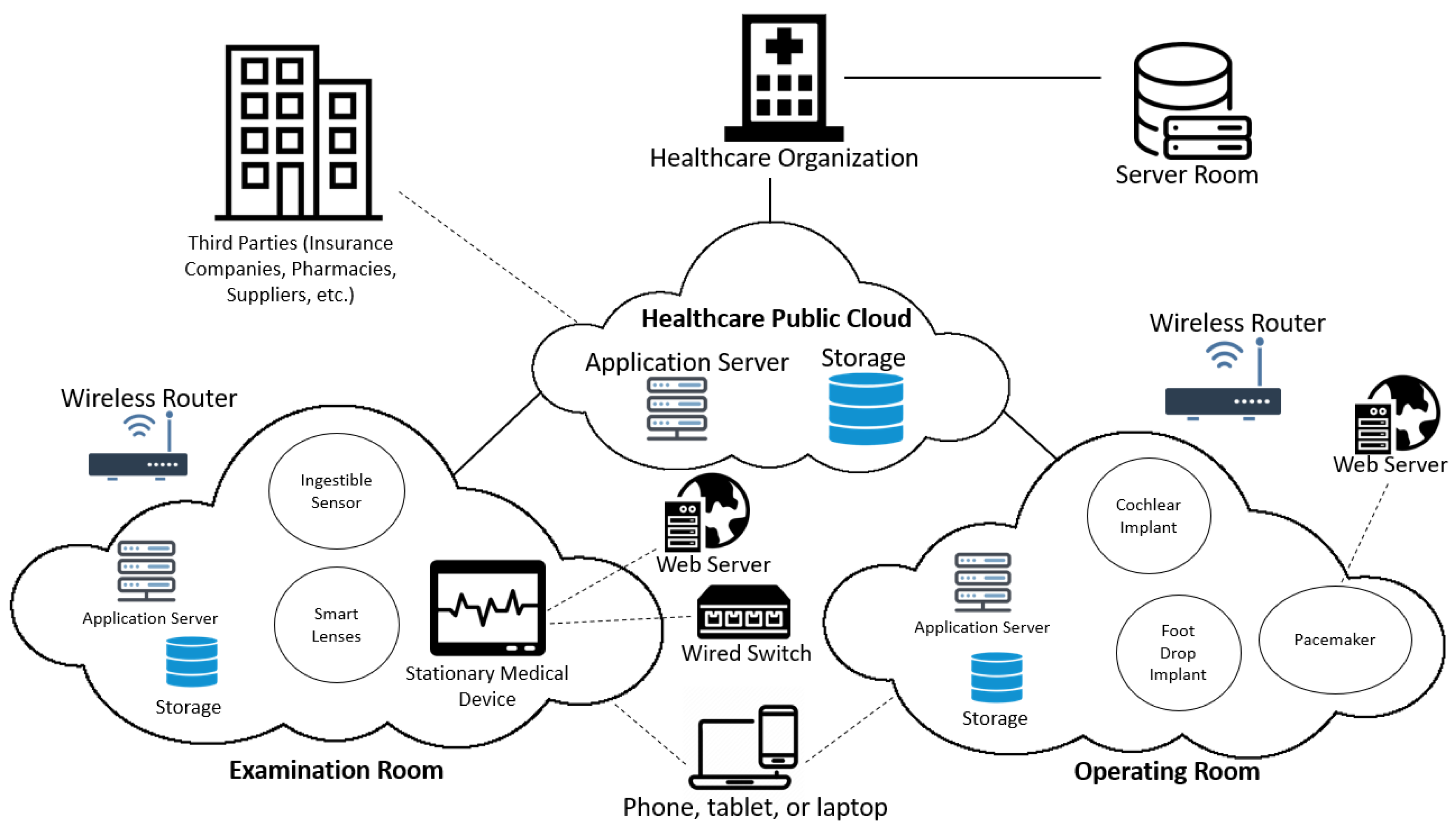
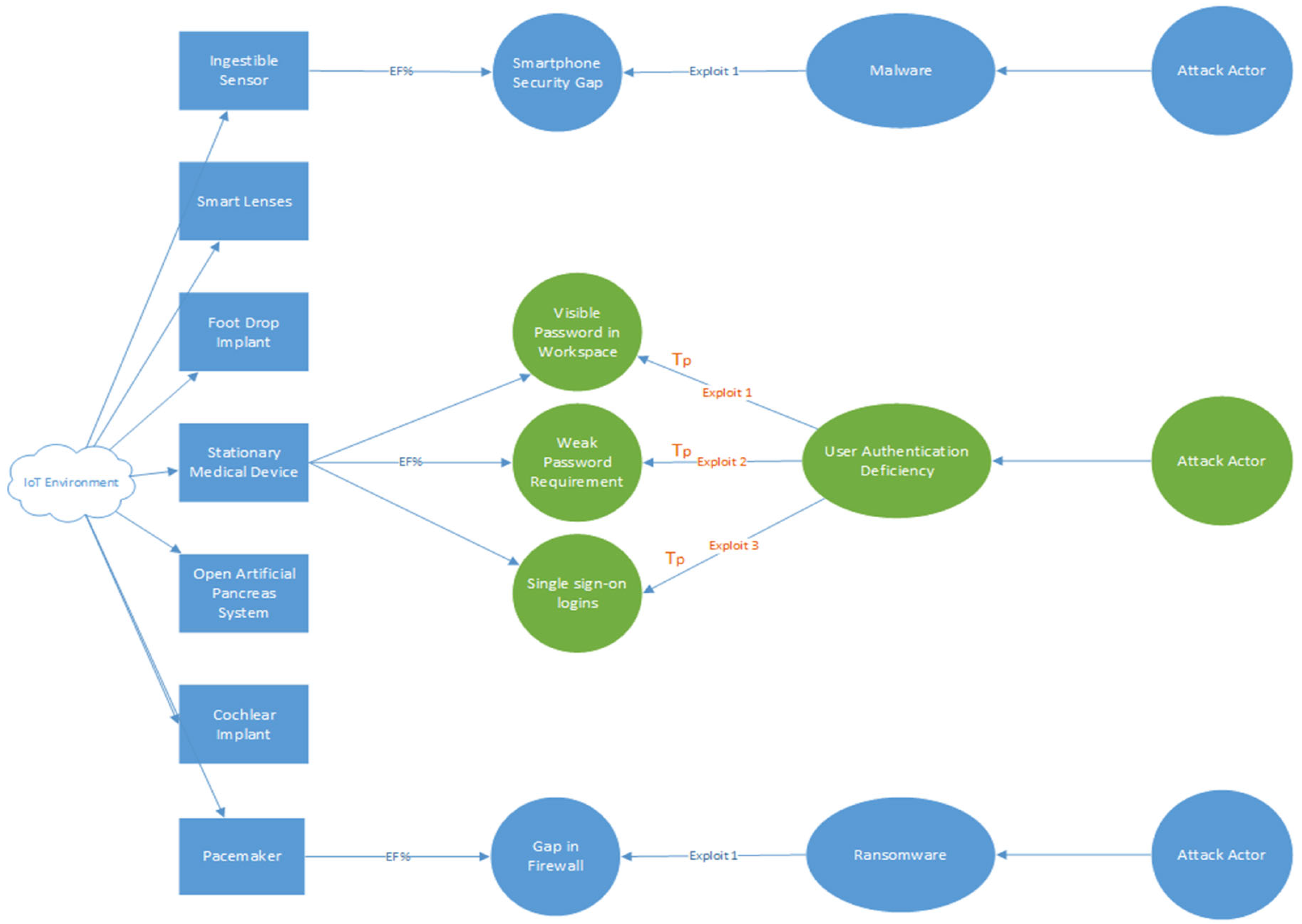
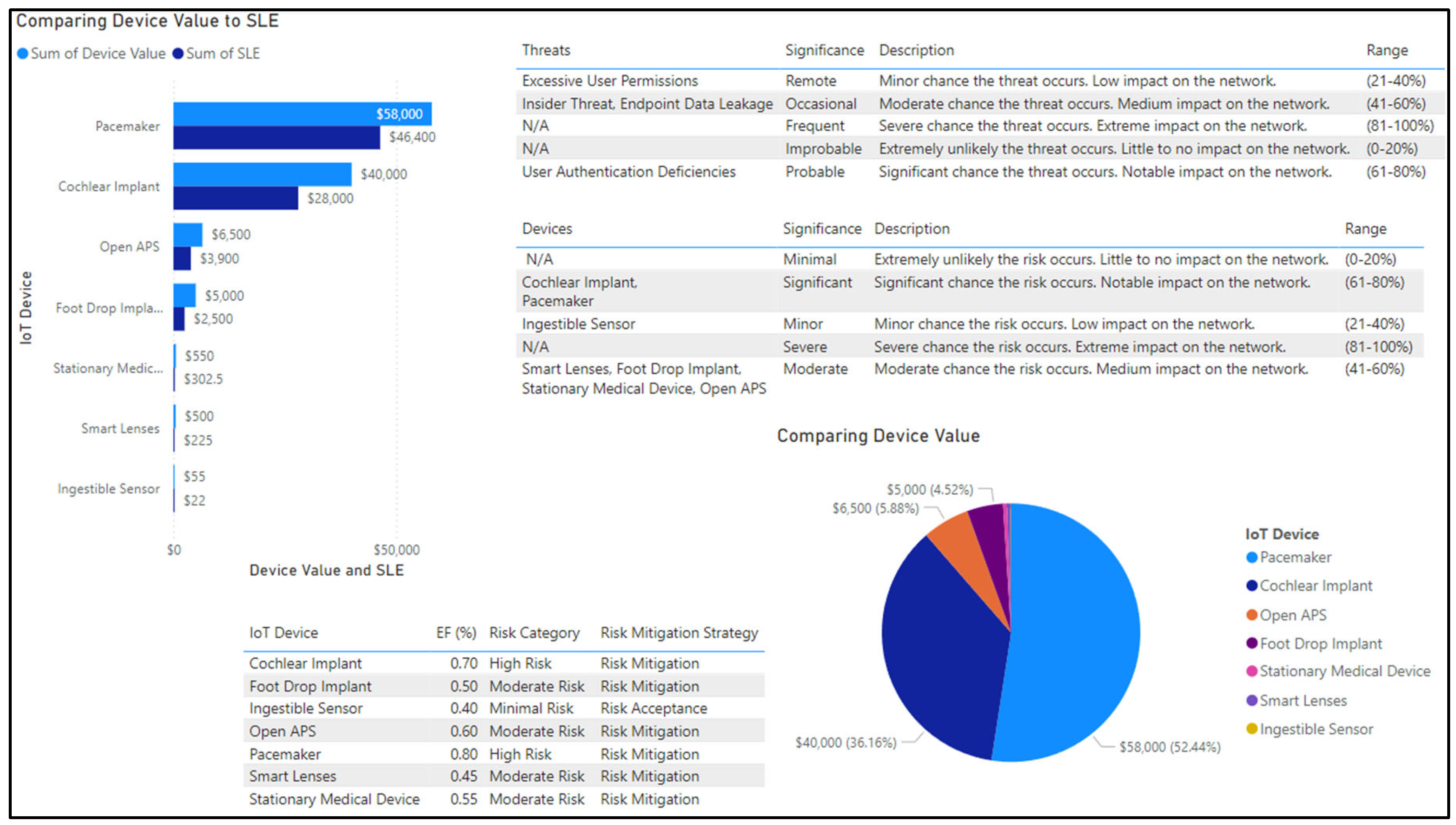
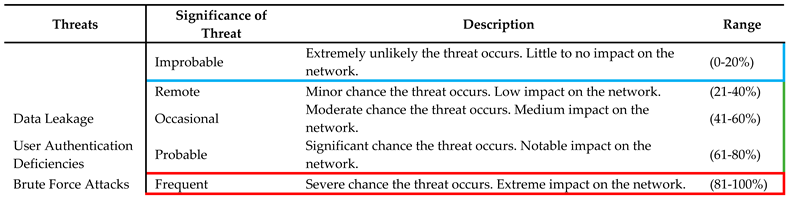
4.2. Healthcare Scenario
4.2.1. Risk Identification of Healthcare Network
4.2.2. Risk Evaluation of Healthcare Network
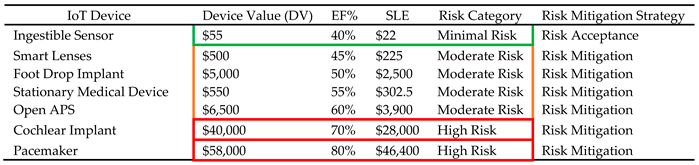
4.2.3. Risk Factor Computations
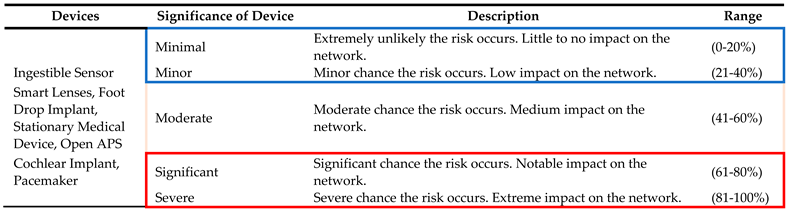
4.2.4. Risk Prioritization of Healthcare IoT Devices
4.2.5. Risk Analysis of Healthcare IoT Devices
4.2.6. Risk Control of Healthcare IoT Devices
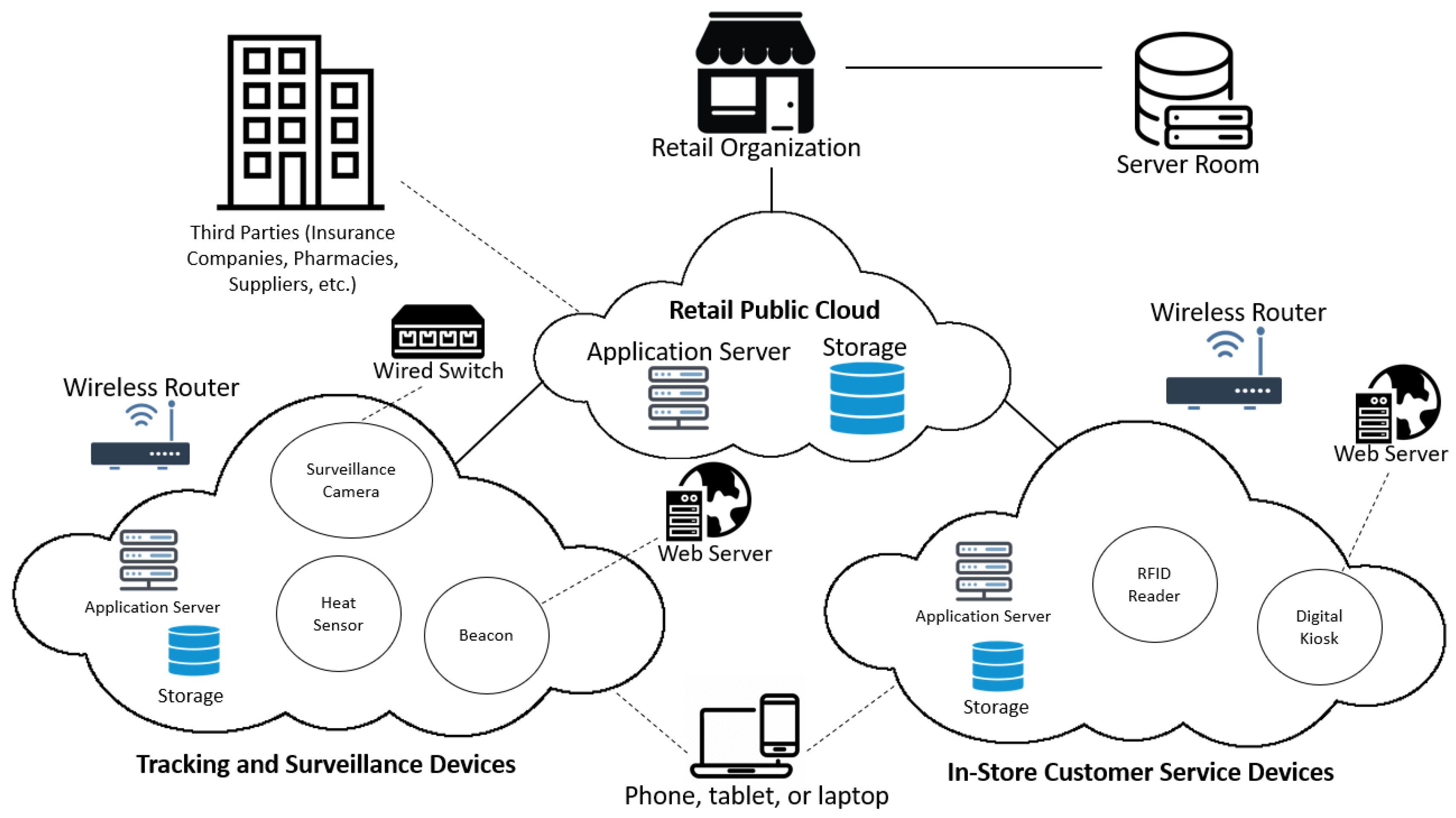
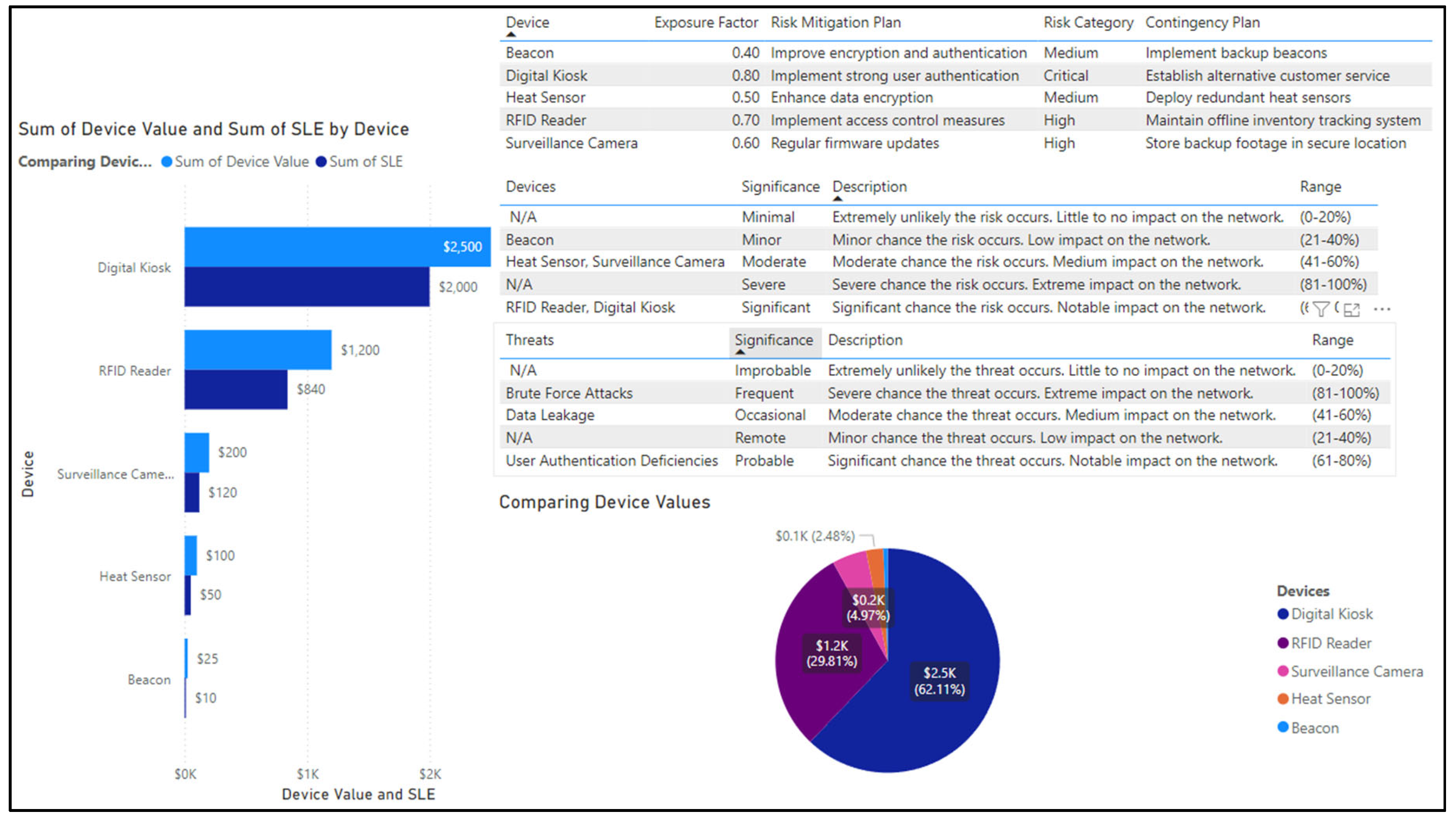
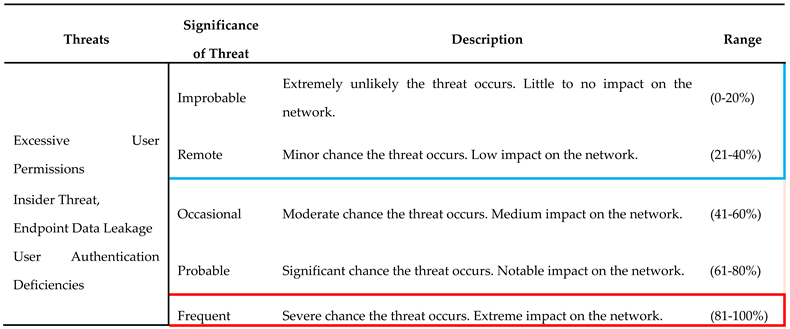
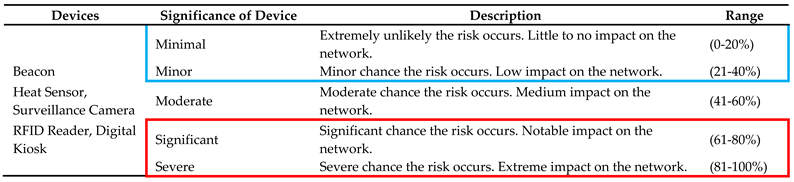
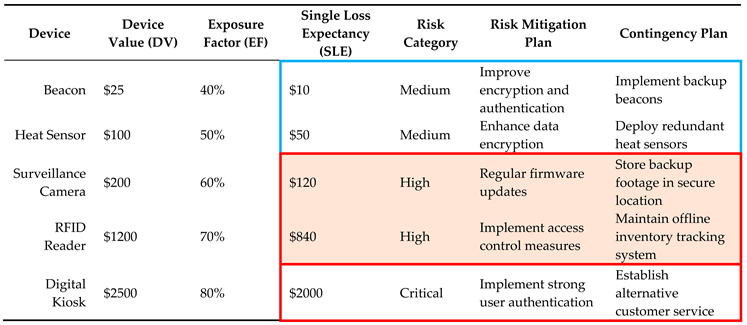
4.3. Retail Scenario
4.3.1. Risk Identification of Retail Organization
4.3.2. Risk Evaluation of Retail Organization
4.3.3. Risk Prioritization of Retail Organization
4.3.4. Risk Analysis of Retail IoT Devices
4.3.5. Risk Control of Retail IoT Devices
5. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Hernandez, B. Xiao and V. Tudor, "ERAIA - Enabling Intelligence Data Pipelines for IoT-based Application Systems," 2020 IEEE International Conference on Pervasive Computing and Communications (PerCom), Austin, TX, USA, 2020, pp. 1-9. [CrossRef]
- Alkali, Yusuf and Routray, Indira and Whig, Pawan, Study of various methods for reliable, efficient and Secured IoT using Artificial Intelligence (January 28, 2022). Proceedings of the International Conference on Innovative Computing & Communication (ICICC) 2022, Available at SSRN: https://ssrn.com/abstract=4020364. [CrossRef]
- Srivastava, A.; Jain, U. , "Securing the Future of IoT: A Comprehensive Framework for Real-Time Attack Detection and Mitigation in IoT Networks," 2023 14th International Conference on Computing Communication and Networking Technologies (ICCCNT), Delhi, India, 2023, pp. 1-6. [CrossRef]
- Choo, K.-K.R.; Gai, K.; Chiaraviglio, L.; Yang, Q. (2021). A multidisciplinary approach to Internet of Things (IoT) cybersecurity and risk management. Computers & Security, 102, 102136. [CrossRef]
- Gómez, G.; Espina, E.; Armas-Aguirre, J.; Molina, J.M.M. , "Cybersecurity architecture functional model for cyber risk reduction in IoT based wearable devices," 2021 Congreso Internacional de Innovación y Tendencias en Ingeniería (CONIITI), Bogotá, Colombia, 2021, pp. 1-4. [CrossRef]
- Kandasamy, K.; Srinivas, S.; Achuthan, K.; Rangan, V.P. (2020). IoT cyber risk: a holistic analysis of cyber risk assessment frameworks, risk vectors, and risk ranking process. EURASIP Journal on Information Security, 2020(1). [CrossRef]
- Edhrabooh, K.M.; Al-Alawi, A.I., "AI and ML Applications in Supply Chain Management Field: A Systematic Literature Review," 2024 ASU International Conference in Emerging Technologies for Sustainability and Intelligent Systems (ICETSIS), Manama, Bahrain, 2024, pp. 202-206. [CrossRef]
- Kuzlu, M.; Fair, C.; Guler, O. (2021). Role of Artificial Intelligence in the Internet of Things (IoT) cybersecurity. Discover Internet of Things, 1(1). [CrossRef]
- Wang, L. , "Application of Machine Learning in Risk Assessment of Big Data IOT Credit Financial Management of Operator," 2022 2nd International Conference on Networking Systems of AI (INSAI), Shanghai, China, 2022, pp. 228-232. [CrossRef]
- Almahairah, M.S.Z.; Goswami, S.; Karri, P.N.; Krishna, I.M.; Aarif, M.; Manoharan, G. , "Application of Internet of Things and Big Data in Improving Supply Chain Financial Risk Management System," 2023 10th IEEE Uttar Pradesh Section International Conference on Electrical, Electronics and Computer Engineering (UPCON), Gautam Buddha Nagar, India, 2023, pp. 276-280. [CrossRef]
- Waqdan, M.; Louafi, H.; Mouhoub, M. , "An IoT Security Risk Assessment Framework for Healthcare Environment," 2023 International Symposium on Networks, Computers and Communications (ISNCC), Doha, Qatar, 2023, pp. 01-08. [CrossRef]
- NIST. (2018). Risk management framework for information systems and organizations: Risk Management Framework for Information Systems and Organizations, 2(Revision 2). [CrossRef]
- Karie, N.M.; Sahri, N.M.; Yang, W.; Valli, C.; Kebande, V.R. , "A Review of Security Standards and Frameworks for IoT-Based Smart Environments," in IEEE Access, vol. 9, pp. 121975-121995, 2021. [CrossRef]
- Thirumagal, P.G.; Vaddepalli, S.; Das, T.; Das, S.; Madem, S.; Immaculate, P.S. , "AI-Enhanced IoT Data Analytics for Risk Management in Banking Operations," 2024 5th International Conference on Recent Trends in Computer Science and Technology (ICRTCST), Jamshedpur, India, 2024, pp. 177-181. [CrossRef]
- Muammar, S.; Shehada, D.; Mansoor, W. , "Digital Risk Assessment Framework for Individuals: Analysis and Recommendations," in IEEE Access, vol. 11, pp. 85561-85570, 2023. [CrossRef]
- Surya, S.; Bhuva, D.; Bhuva, A.; Chavan, S.S.; Basha, D.K.; Chattopadhyay, S. , "Implementation of Internet of Things (IoT) framework for Governing Modern Cyber Attacks in Computer Network," 2023 IEEE International Conference on ICT in Business Industry & Government (ICTBIG), Indore, India, 2023, pp. 1-5. [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




