Submitted:
04 February 2026
Posted:
04 February 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Research Background
1.2. Security by Design
1.3. Research Gap and Purpose of the Study
2. Literature Review
2.1. CARVER—History, Applications, Limitations
2.2. BIM in the Context of Security
2.3. Existing Risk Assessment Methods in BIM
3. Methodology
3.1. BIM–CARVER (Design Science Research)
3.2. Conceptual Assumptions
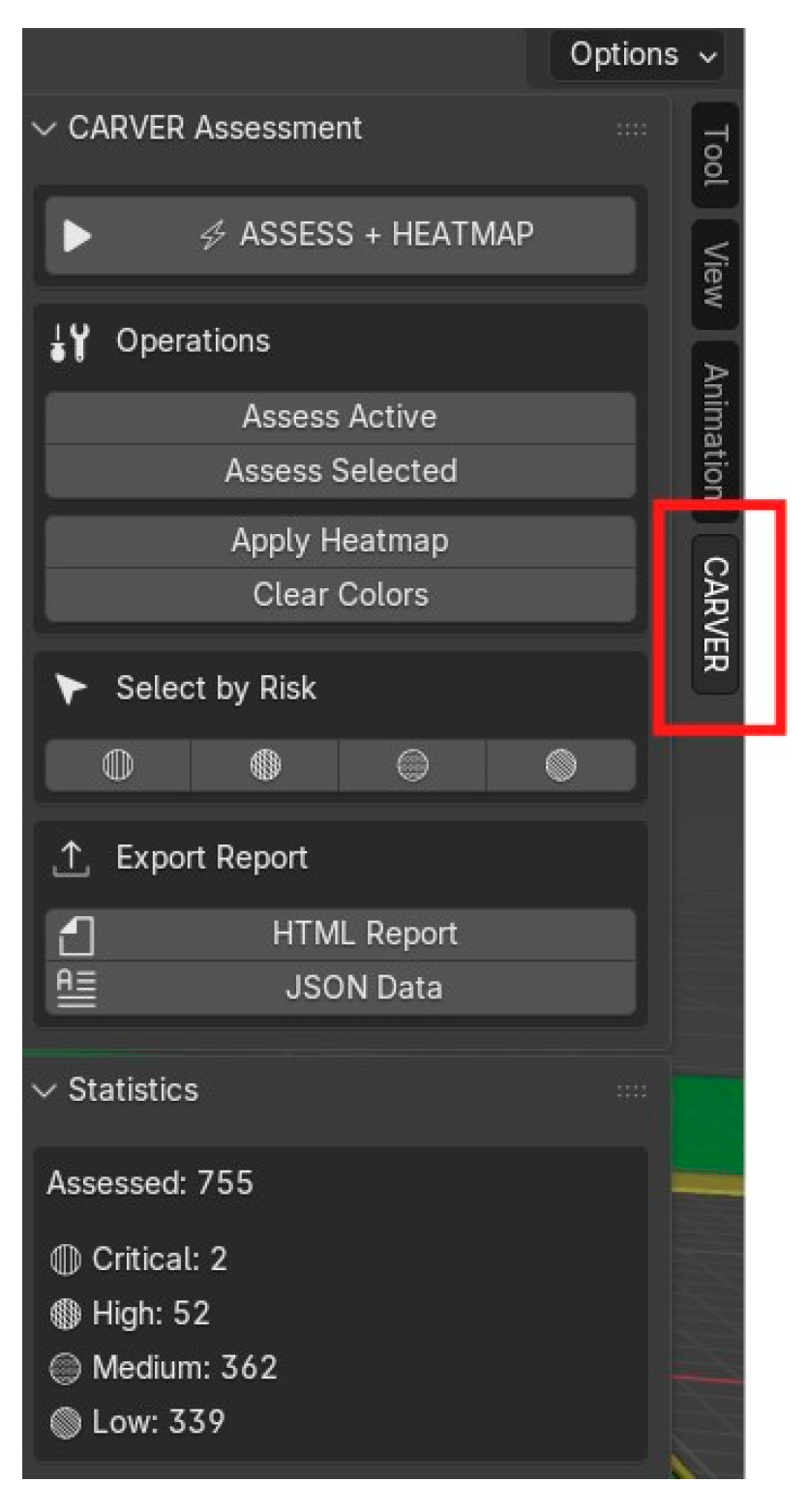
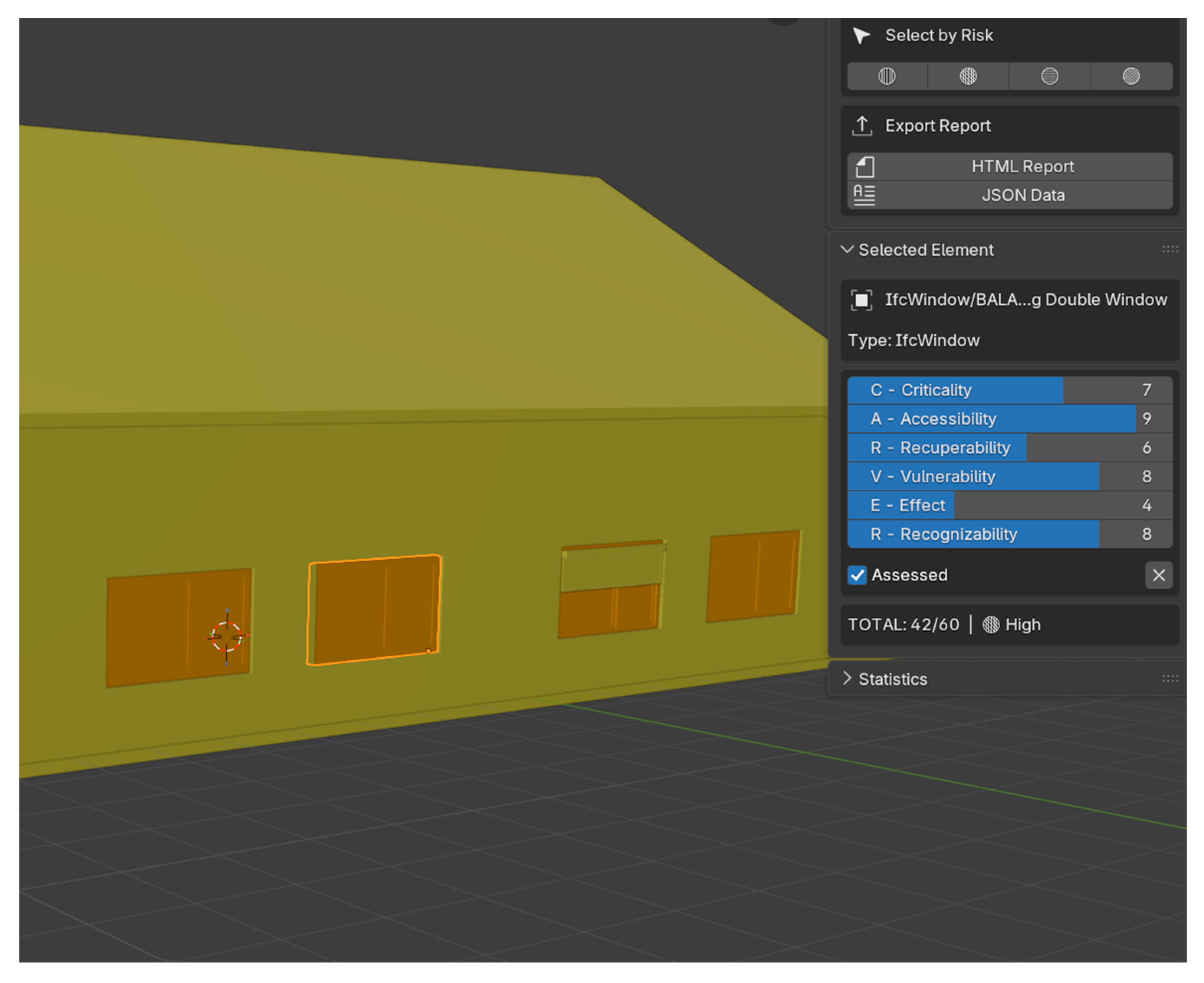
3.3. Plugin Components
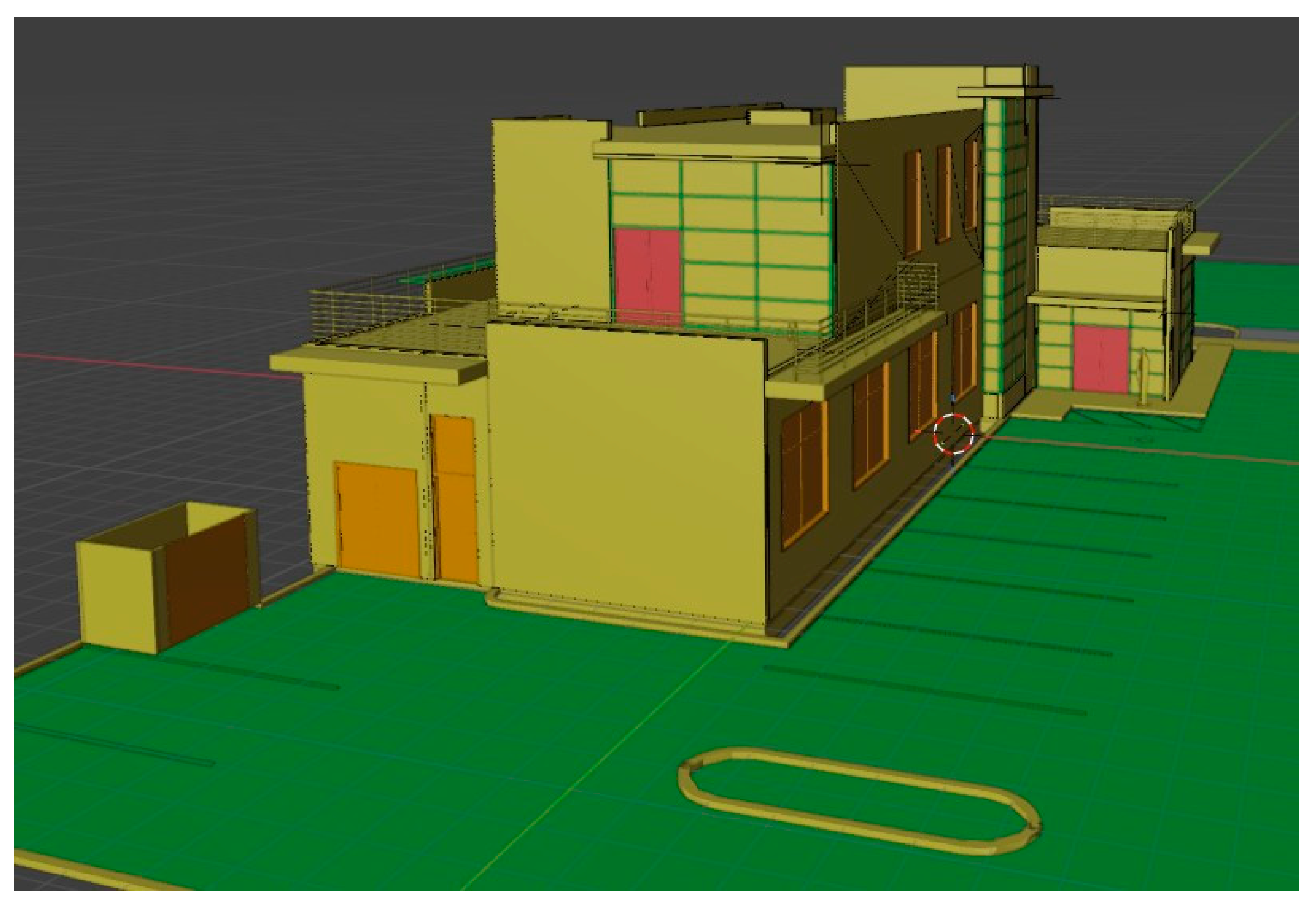
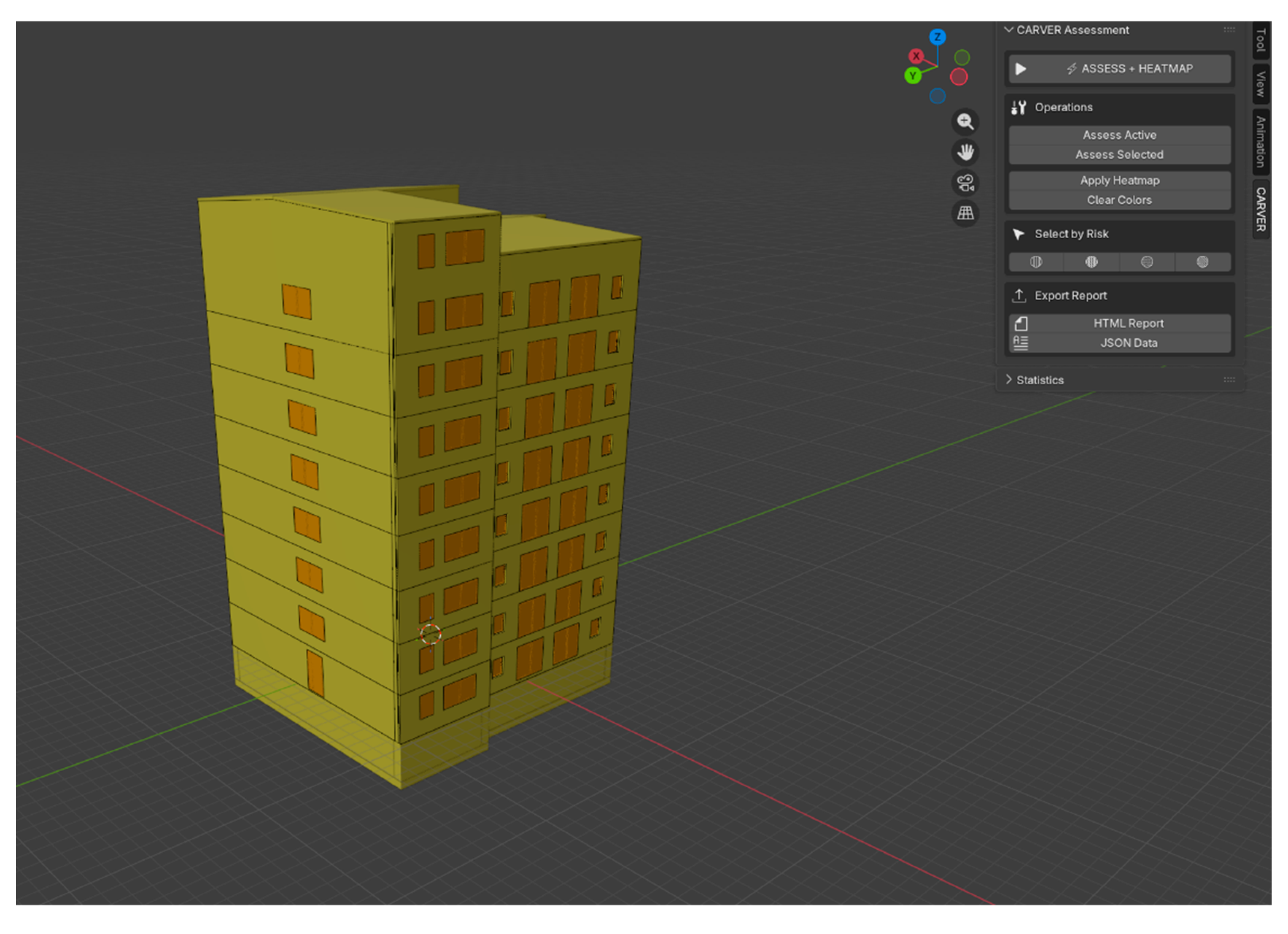
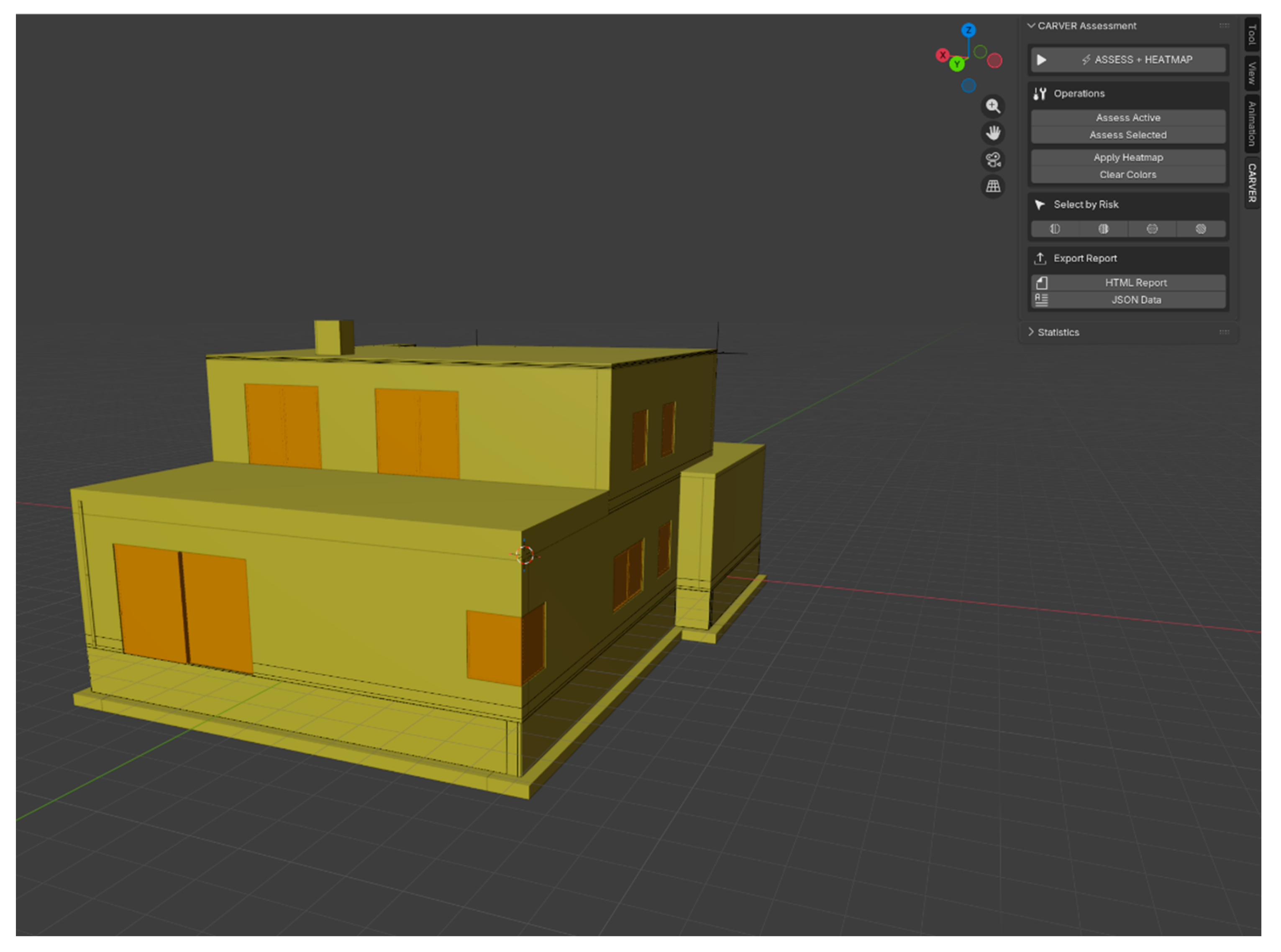
4. Results and Case Study
4.1. Identification of Critical Elements
4.2. CARVER Assessment for Each Element
4.3. Tool Validation
4.4. Selected Comparison of Design Variants in Terms of Aggregate Risk
5. Discussion and Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Fennelly, L.J. Effective Physical Security, 5th ed.; Butterworth-Heinemann: Oxford, UK, 2017. [Google Scholar]
- Garcia, M.L. The Design and Evaluation of Physical Protection Systems, 2nd ed.; Butterworth-Heinemann: Burlington, MA, USA, 2008. [Google Scholar]
- MacLeamy, P. Collaboration, Integrated Information and the Project Lifecycle in Building Design, Construction and Operation. The Construction Users Roundtable (CURT), 2004; pp. WP–1202. [Google Scholar]
- Borkowski, A.S.; Drozd, W.; Zima, K. The Status of the Implementation of the Building Information Modeling Mandate in Poland: A Literature Review. ISPRS Int. J. Geo-Inf. 2024, 13, 343. [Google Scholar] [CrossRef]
- Borkowski, A.S. Digital Twin Conceptual Framework for the Operation and Maintenance Phase in the Building’s Lifecycle. Arch. Civ. Eng. 2024, 70, 139–152. [Google Scholar] [CrossRef]
- BSI. PAS 1192-5:2015 Specification for Security-Minded Building Information Modeling, Digital Built Environments and Smart Asset Management. British Standards Institution: London, UK, 2015.
- Bencie, L.; Labaj, L. The CARVER Target Analysis and Vulnerability Assessment Methodology; Security Management International: Washington, DC, USA, 2018. [Google Scholar]
- U.S. Army. FM 34-36 Special Operations Forces Intelligence and Electronic Warfare Operations; Department of the Army: Washington, DC, USA, 1991. [Google Scholar]
- Pärn, E.A.; Edwards, D.J.; Sing, M.C.P. The building information modeling trajectory in facilities management: A review. Autom. Constr. 2017, 75, 45–55. [Google Scholar] [CrossRef]
- Boje, C.; Guerriero, A.; Kubicki, S.; Rezgui, Y. Towards a semantic Construction Digital Twin: Directions for future research. Autom. Constr. 2020, 114, 103179. [Google Scholar] [CrossRef]
- CISA. Infrastructure Security Division Strategic Plan 2019–2022; Cybersecurity and Infrastructure Security Agency: Washington, DC, USA, 2019. [Google Scholar]
- buildingSMART International. Industry Foundation Classes (IFC) Specification. Available online: https://www.buildingsmart.org/standards/bsi-standards/industry-foundation-classes/ (accessed on 15 December 2024).
- Nadel, B.A. Building Security: Handbook for Architectural Planning and Design; McGraw-Hill: New York, NY, USA, 2004. [Google Scholar]
- Del-Real, C.; De Busser, E.; van den Berg, B. Shielding software systems: A comparison of security by design and privacy by design based on a systematic literature review. Comput. Law Secur. Rev. 2023, 49, 105933. [Google Scholar] [CrossRef]
- Borkowski, A.S.; Maroń, M. Semantic Enrichment of Non-Graphical Data of a BIM Model of a Public Building from the Perspective of the Facility Manager. Big Data Cogn. Comput. 2024, 8, 138. [Google Scholar] [CrossRef]
- Cheng, M.Y.; Chiu, K.C.; Hsieh, Y.M.; Yang, I.T.; Chou, J.S. BIM integrated smart monitoring technique for building fire prevention and disaster relief. Autom. Constr. 2017, 84, 14–30. [Google Scholar] [CrossRef]
- Greaver, B.S.; Raabe, L.; Fox, W.P.; Burks, R.E. CARVER 2.0: Integrating the Analytical Hierarchy Process's multi-attribute decision-making weighting scheme for a center of gravity vulnerability analysis for US Special Operations Forces. J. Def. Model. Simul. 2018, 15, 111–120. [Google Scholar] [CrossRef]
- Couretas, J.M. Cyber Offense and Targeting. In An Introduction to Cyber Analysis and Targeting; Springer: Cham, Switzerland, 2022; pp. 145–178. [Google Scholar]
- Liu, C.; Tay, S.K. The Security Risk Assessment Methodology. Procedia Eng. 2012, 43, 600–609. [Google Scholar] [CrossRef]
- Sidani, A.; Martins, J.; Soeiro, A. BIM Best Practices for Construction Health and Safety: A Systematic Review. Available at SSRN. 2023, 4595455. [Google Scholar]
- Sun, Q.; Turkan, Y. A BIM-based simulation framework for fire safety management and investigation of the critical factors affecting human evacuation performance. Adv. Eng. Inform. 2020, 44, 101093. [Google Scholar] [CrossRef]
- Deng, H.; Ou, Z.; Zhang, G.; Deng, Y.; Tian, M. BIM and Computer Vision-Based Framework for Fire Emergency Evacuation Considering Local Safety Performance. Sensors 2021, 21, 3851. [Google Scholar] [CrossRef]
- Labadan, R.; Panuwatwanich, K.; Takahashi, S. Building Information Modeling for Prevention through Design: An Exploratory Structural Model of Factors Influencing Its Adoption. J. Constr. Dev. Ctries. 2025, 30, 221–246. [Google Scholar] [CrossRef]
- Das, M.; Tao, X.; Cheng, J.C.P. BIM security: A critical review and recommendations using encryption strategy and blockchain. Autom. Constr. 2021, 126, 103682. [Google Scholar] [CrossRef]
- Solihin, W.; Eastman, C. Classification of Rules for Automated BIM Rule Checking Development. Autom. Constr. 2015, 53, 69–82. [Google Scholar] [CrossRef]
- Lu, Y.; Gong, P.; Tang, Y.; Sun, S.; Li, Q. BIM-Integrated Construction Safety Risk Assessment at the Design Stage of Building Projects. Autom. Constr. 2021, 124, 103553. [Google Scholar] [CrossRef]
- Drozd, W.; Kowalik, M. A Study on the State of Knowledge of Managers of Construction Sites in the Field of Occupational Safety. MATEC Web Conf. 2019, 262, 07001. [Google Scholar] [CrossRef]
- Hossain, M.A.; Abbott, E.L.S.; Chua, D.K.H.; Nguyen, T.Q.; Goh, Y.M. Design-for-Safety Knowledge Library for BIM-Integrated Safety Risk Reviews. Autom. Constr. 2018, 94, 290–302. [Google Scholar] [CrossRef]
- Peng, J.; Liu, X. Automated Code Compliance Checking Research Based on BIM and Knowledge Graph. Sci. Rep. 2023, 13, 7065. [Google Scholar] [CrossRef]
- Kładź, M.; Borkowski, A.S. IDS Standard and bSDD Service as Tools for Automating Information Exchange and Verification in Projects Implemented in the BIM Methodology. Buildings 2025, 15, 378. [Google Scholar] [CrossRef]
- Zima, K.; Mitera-Kiełbasa, E. Employer's Information Requirements: A Case Study Implementation of BIM on the Example of Selected Construction Projects in Poland. Appl. Sci. 2021, 11, 10587. [Google Scholar] [CrossRef]
- Siewczyński, B.; Szot, J. Analytical aspects of BIM technology in the architectural education process. A case study from the Poznań University of Technology. Scientific Journal of the Poznań University of Technology. Architecture, Urban Planning, Interior Design (in Polish). 2023, 14, 119–129. [Google Scholar]
- Warchoł, A. The Concept of LiDAR Data Quality Assessment in the Context of BIM Modeling. Int. Arch. Photogramm. Remote Sens. Spat. Inf. Sci. 2019, XLII-1/W2, 61–66. [Google Scholar] [CrossRef]


| No. | Building Type | Total Assessed | Average Score [6-60] | Critical [%] | High [%] | Medium [%] | Low [%] |
|---|---|---|---|---|---|---|---|
| 1. | Single-family | 104 | 29.7 | 0 | 17.3 | 82.7 | 0 |
| 2. | Multi-family | 249 | 33.8 | 0 | 55.2 | 47.8 | 0 |
| 3. | Multi-family | 236 | 24.8 | 0 | 16.5 | 67.4 | 16.1 |
| 4. | Multi-family | 425 | 23.9 | 0 | 10.1 | 51.8 | 38.1 |
| 5 | Commercial | 6020 | 23.5 | 0 | 6.0 | 58.7 | 35.4 |
| 6. | Single-family | 116 | 29.4 | 0 | 23.3 | 76.7 | 0 |
| 7. | Single-family | 65 | 29.1 | 0 | 23.1 | 76.9 | 0 |
| 8. | Single-family | 123 | 27.1 | 0 | 12.2 | 87.8 | 0 |
| 9. | Single-family | 392 | 22.1 | 0 | 1.5 | 88.0 | 10.5 |
| 10. | Commercial | 5547 | 21.1 | 0 | 2.8 | 31.9 | 65.2 |
| Mean [%] | — | 1327.7 | 26.5 | 0 | 16.5 | 67 | 16.5 |
| Element | Variant | C | A | R | V | E | R | Score [6-60] |
| Window 1 | A | 4 | 7 | 6 | 8 | 4 | 7 | 36 |
| B | 7 | 9 | 6 | 8 | 4 | 8 | 42 | |
| C | 4 | 7 | 6 | 9 | 4 | 7 | 37 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.




